In the LinkedIn ArchiMate posting Difference between business/application/technology process?, Anna Aaltonen asked:
“Does someone have good examples how elements Technology process and Application process differ? Maybe comparing also to element Business process. Basically, processes are the same, no matter how those are executed. Basically moving from higher level models to detailed models is just playing with hierarchy, not changing layer. I am looking for a practical example (preferably an example using all those) as well as some hints how to guide modelers (in practice), when they ask whether they should use this or that.”
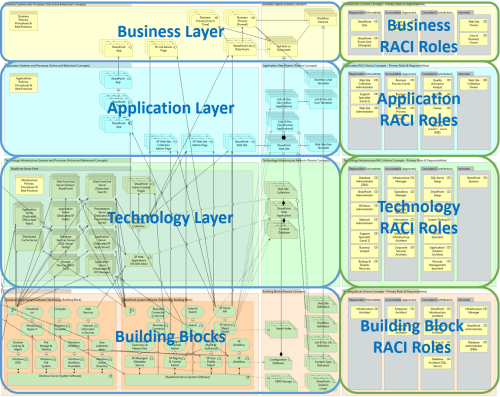
One tip I use to help clarify these type of questions is to think about the constituencies served by each layer in a traditional enterprise architecture model and add the specific list of roles beside (to the right side of) each layer. Below is an example taken from the article ARMs for Metadata-Driven LOB apps: SharePoint 2013/SharePoint 2016.
Figure 1. Enterprise Architecture Layers: Constituencies
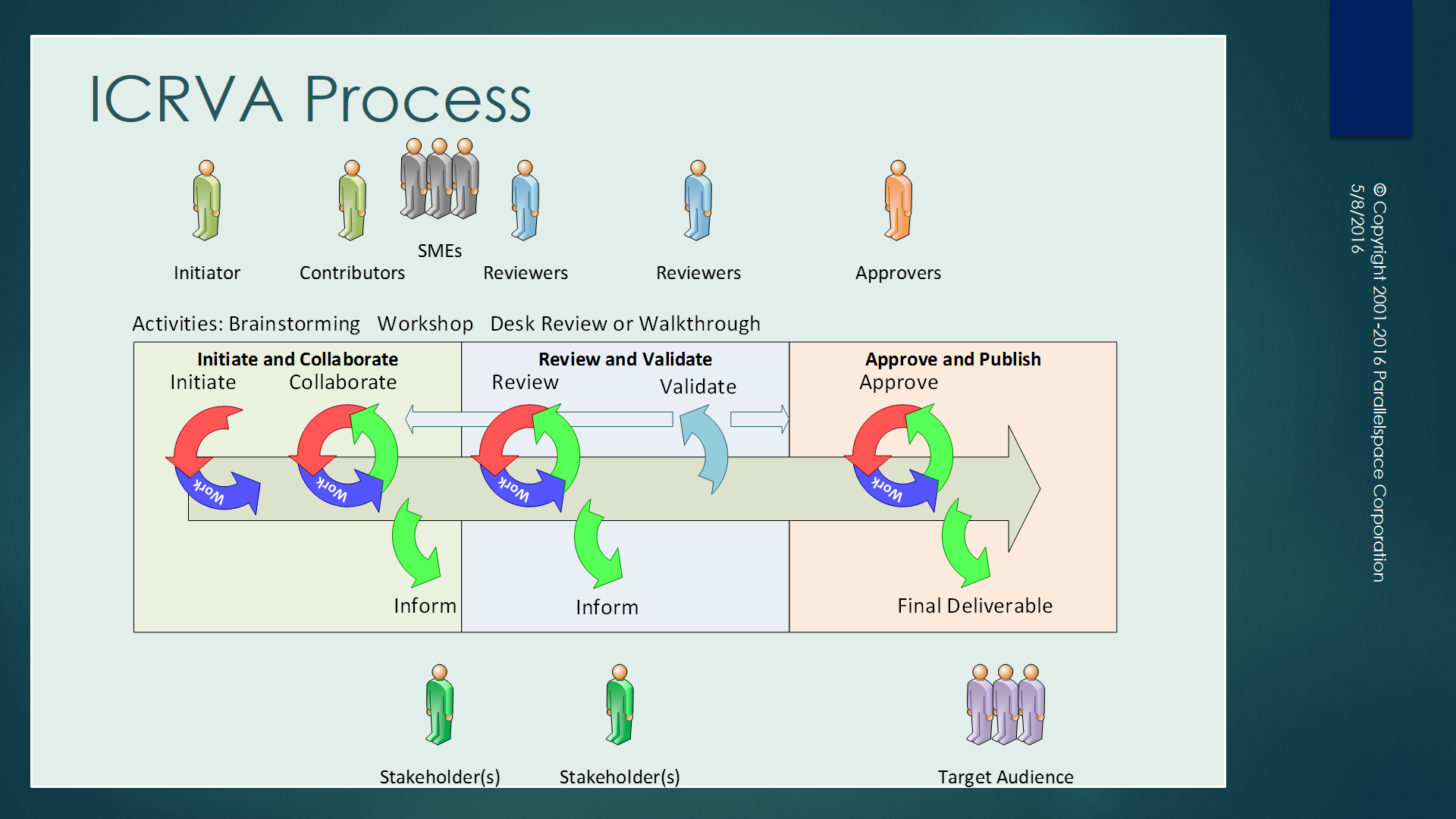
For each of the layers, the list of pertinent roles is listed. I choose to further organize the roles based on RACI categories (also check out this related article):
- Responsible (Deliverables)
- Accountable (Approvers)
- Consulted (Contributors)
- Informed
Linking back to Anna’s question, this approach helps to focus everything that exists in a particular layer relative its constituency. Business Processes serve the needs to the Business architecture layer constituency; Application Processes, the needs of the Application layer constituency layer; Technology Processes, the needs of the Technology layer constituency.
Application Processes include development, testing and maintenance. For Technology Processes, deployment, operations and upgrading are simple examples.
Best regards,
Michael Herman (Toronto)
Parallelspace Corporation
mwherman@parallelspace.net