

Filed under Uncategorized
Copyright (c) 2021-2025 Michael Herman (Alberta, Canada) – Creative Commons Attribution-ShareAlike 4.0 International Public License
https://creativecommons.org/licenses/by-sa/4.0/legalcode
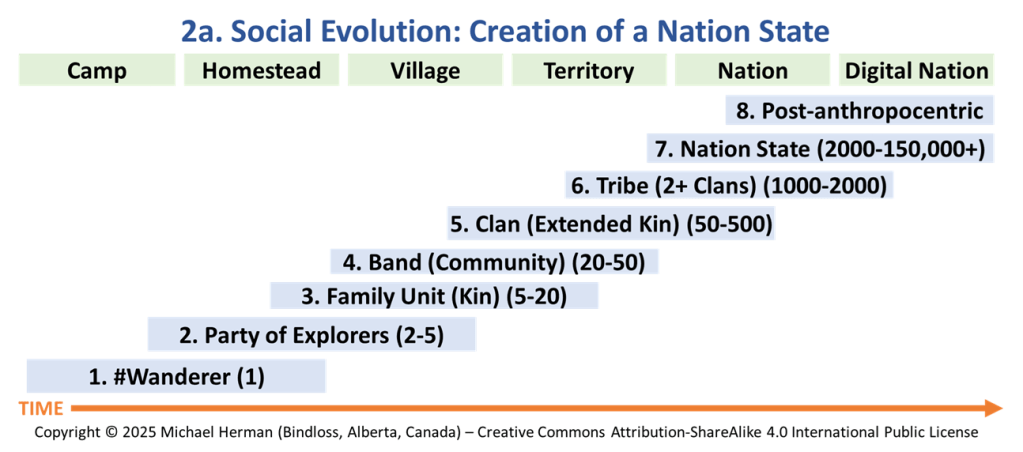
Almost 2 years ago when I created and documented the Social Evolution models for Technology Adoption, I never dreamed that I would be writing an article with the above title.
Paraphrasing, the Social Evolution model states:
A #wanderer is someone who leaves their tribe to share their knowledge and wisdom with others; to later form a party of explorers to explore and conquer a common set of goals; and, even further on, create a clan, a band, a tribe, and a tribal society, a group of people who live and work together – a group of tribes organized around kinships.
The Social Evolution model was first documented (illustrated) here: click Social Evolution and Technology Adoption.
Later, the model was added to the list of what became 2 of the 20+ models in the article: Technology Adoption Models: A Comprehensive Guide as:
Model 2a appears below followed by Model 2b.
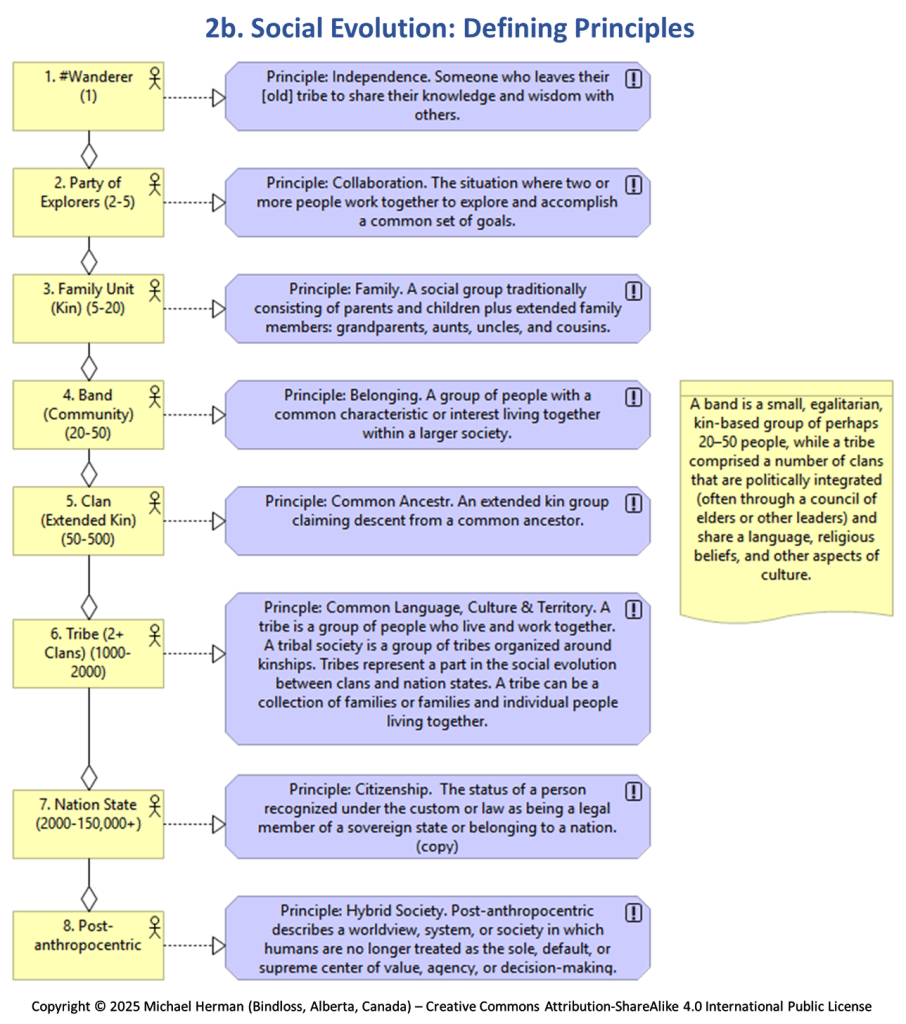
What I didn’t realize is that I was also defining a framework for a new political spectrum:
…and hence, a new Social Evolution model.

Is the Social Evolution model harmful? No, not at all …as long as it remains helpful in illuminating new concepts like the Self-Sovereignty Political Spectrum.
What is your self-sovereignty political affiliation? Are you:
…or are you a centrist?
Have a great day.
“The mind once enlightened, cannot be darkened” – Thomas Paine
Filed under Uncategorized
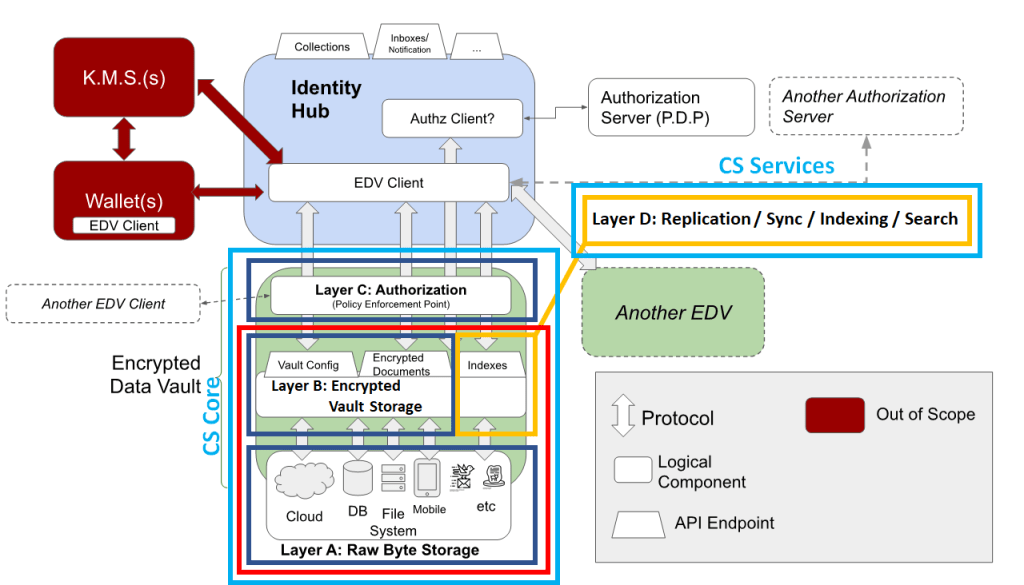
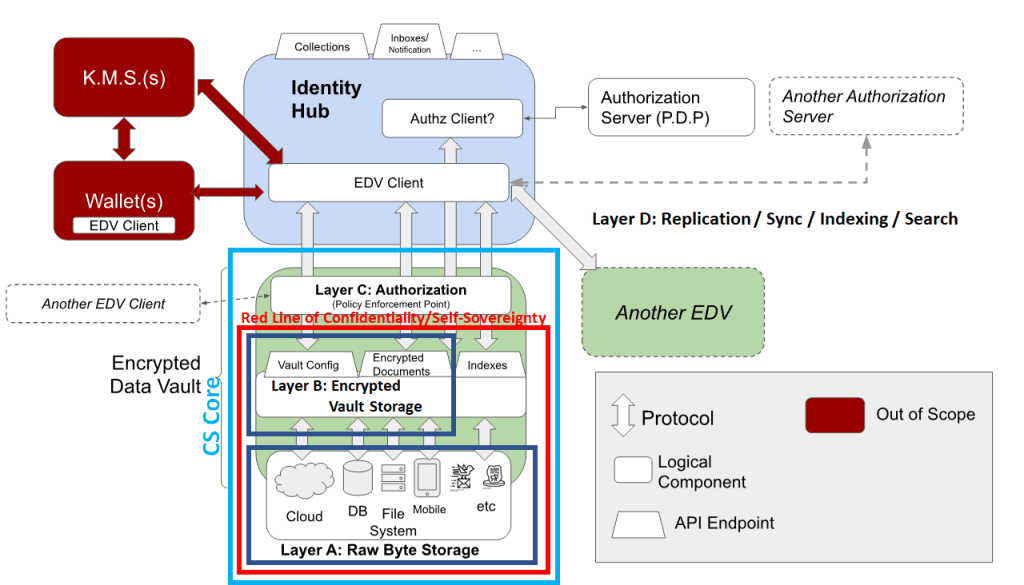
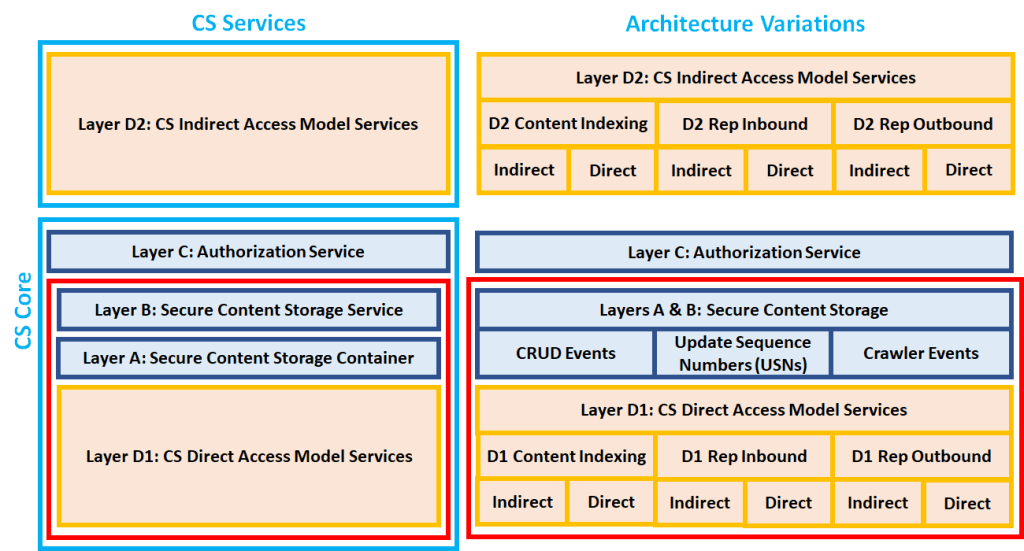
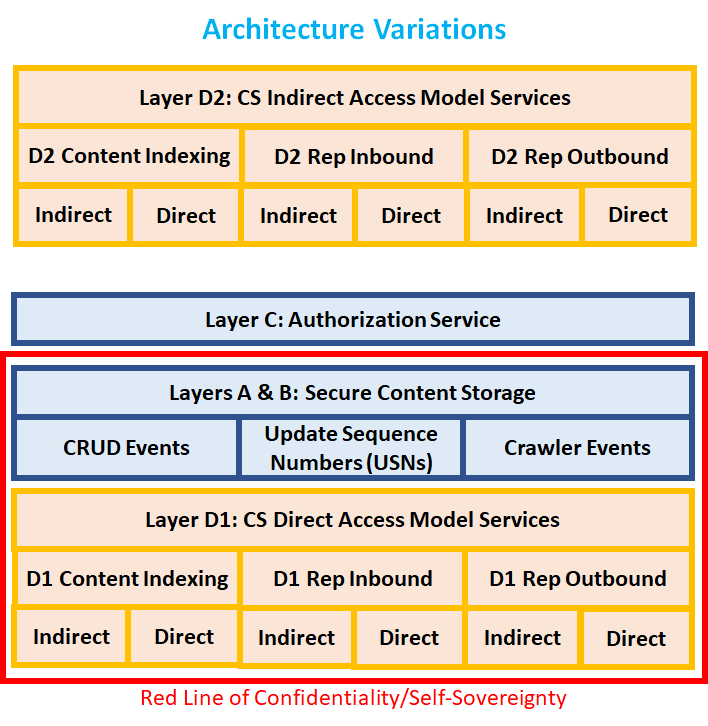
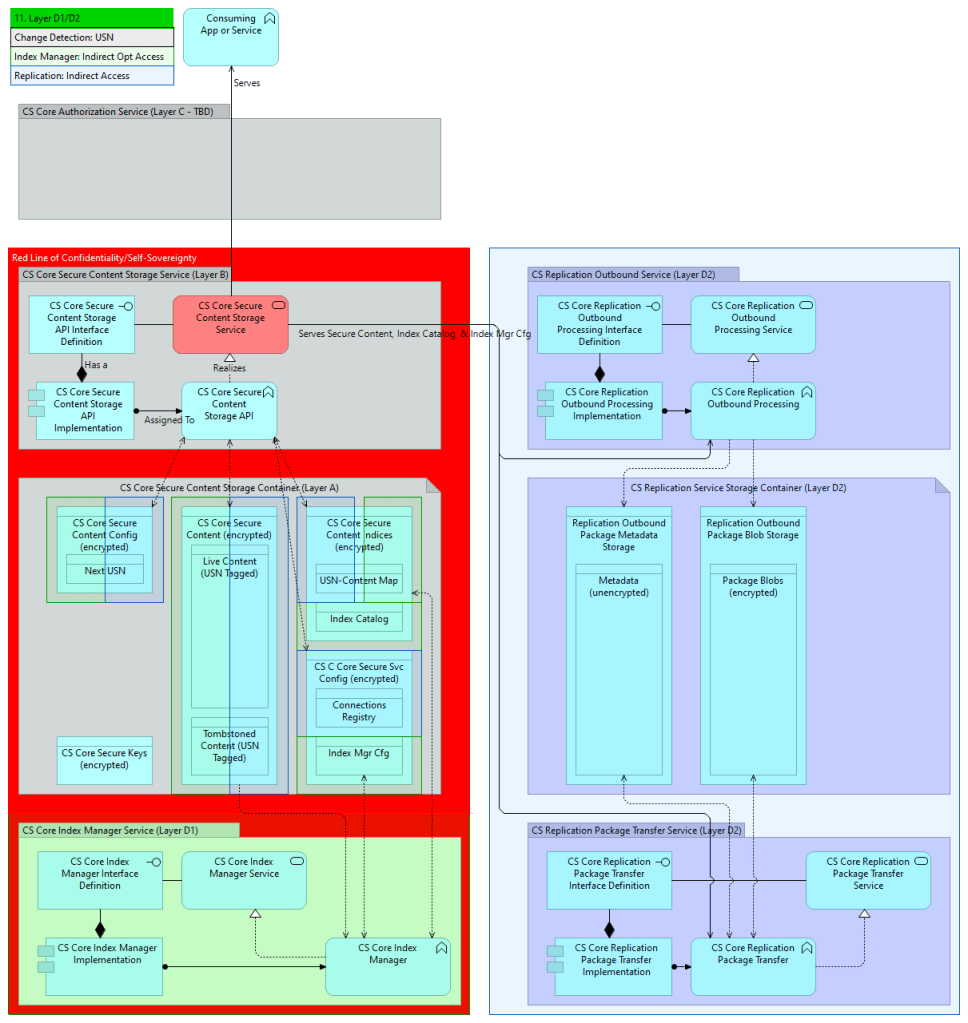
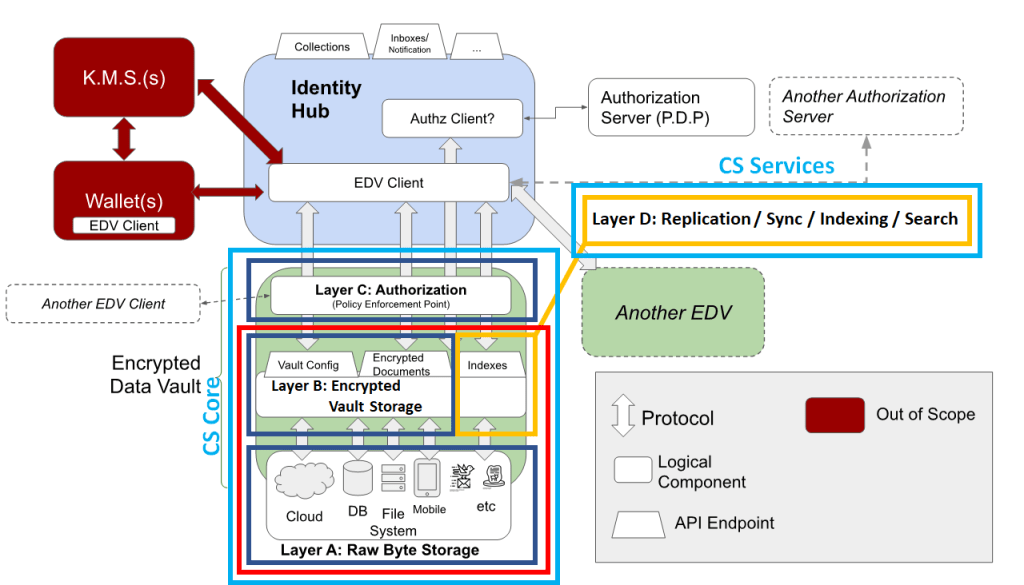
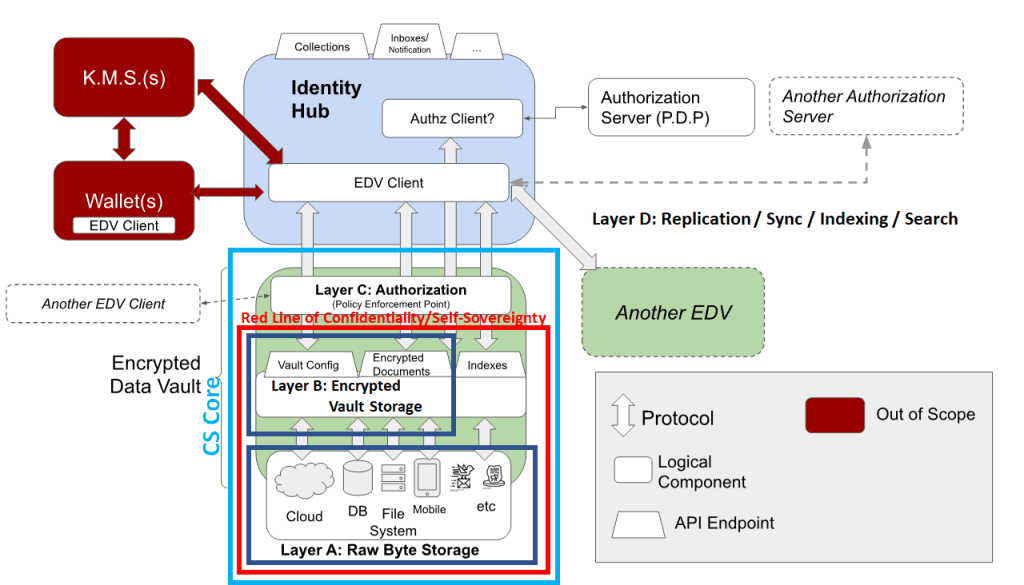
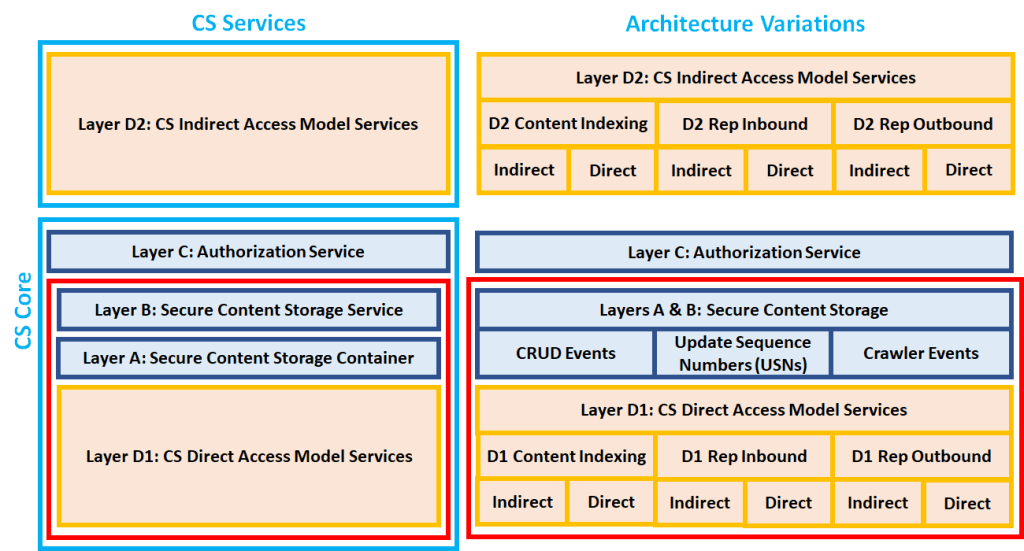
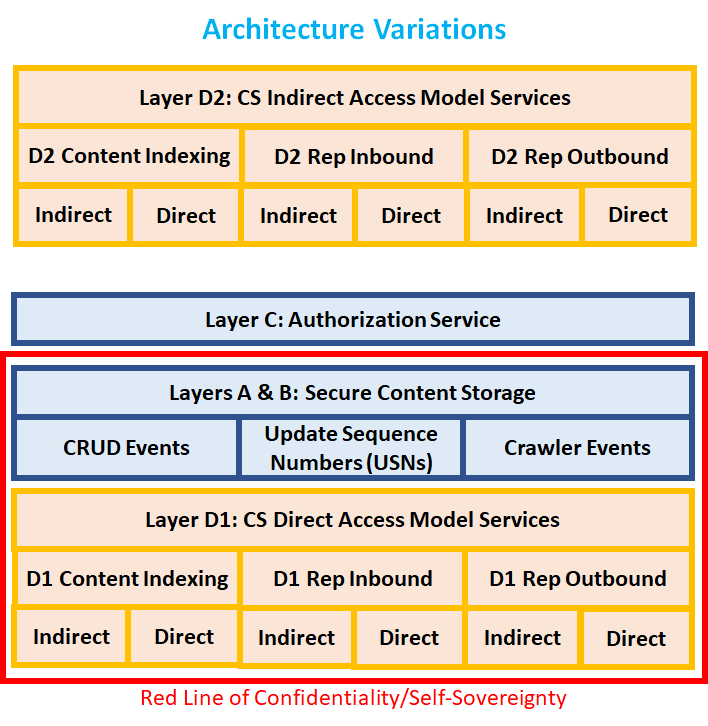
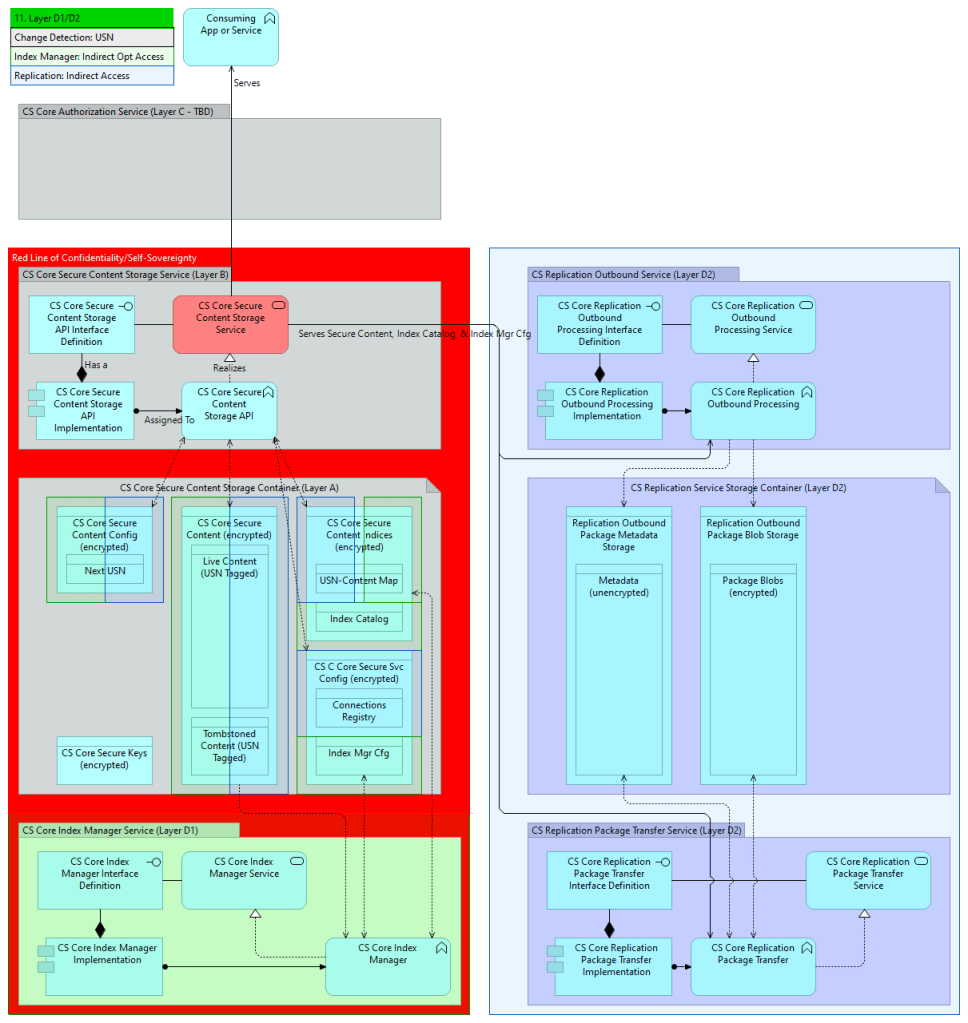
This is a concept architecture diagram for a hypothetical design based on:
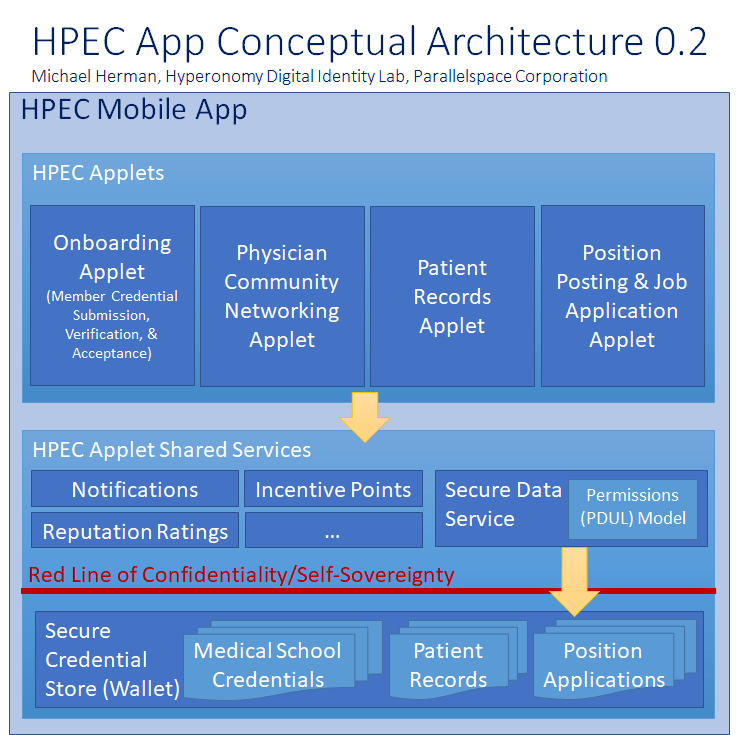
From: Self-Sovereign Identity Personal Data Usage Licensing (SSI-PDUL) Model: Solution Concept whitepaper
Self-Sovereign Identity, as a standalone phrase or as an acronym (SSI), is a very confusing, overloaded, ambiguous term whose use should be avoided in all situations[1]. In a conversation, a blog post, an article, or a standards document, it could mean any of the uncontracted terms in the following figure.
[1] The most recent example of SSI confusion is the Principles of SSI document published by the Sovrin Foundation (https://sovrin.org/principles-of-ssi/). The document makes no attempt to define SSI nor state what SSI is intended to be an acronym for. Principles of SSI has resulted in a lot of confudsion (https://hyperonomy.com/2018/12/18/definition-confuding/) in the decentralized identifier communities as different working groups try to apply the Principles in new domains without first discerning: a) precisely which definition/application of SSI should be used and b) the types or categories of principles being represented in the document. Without first having a clear and precise definition for (a), successfully achieving (b) is almost impossible.
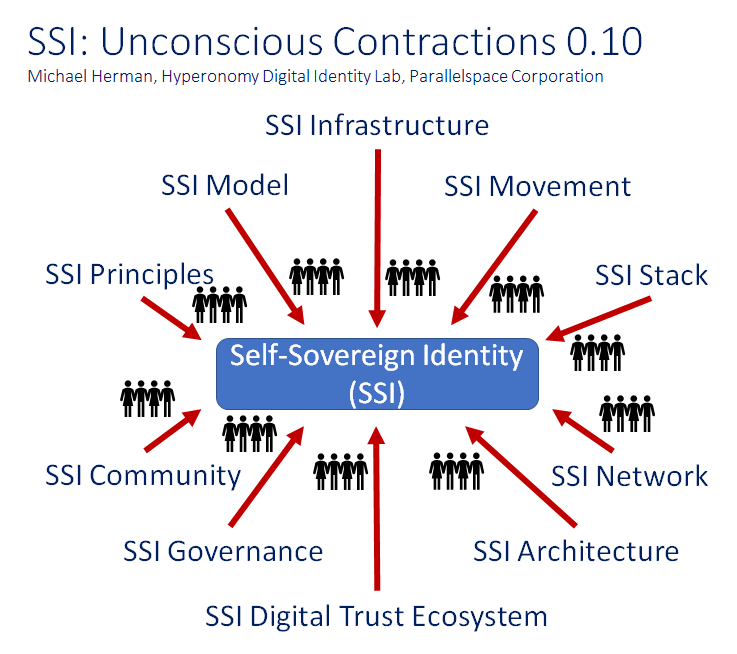
The term Self-Sovereign Identity (or its acronym SSI) could refer to any or all of the uncontracted terms in the above figure – unless an author has taken great care to be clear and precise with respect to every occurrence/usage of the term and/or its acronym.
To understand, in plain English, what a Self-Sovereign Identity (SSI) is, one must first recognize that “Self-Sovereign” is an adjective applied to the noun “Identity”. The TDW Glossary derivation of Self- Sovereign Identity is depicted in the model below.
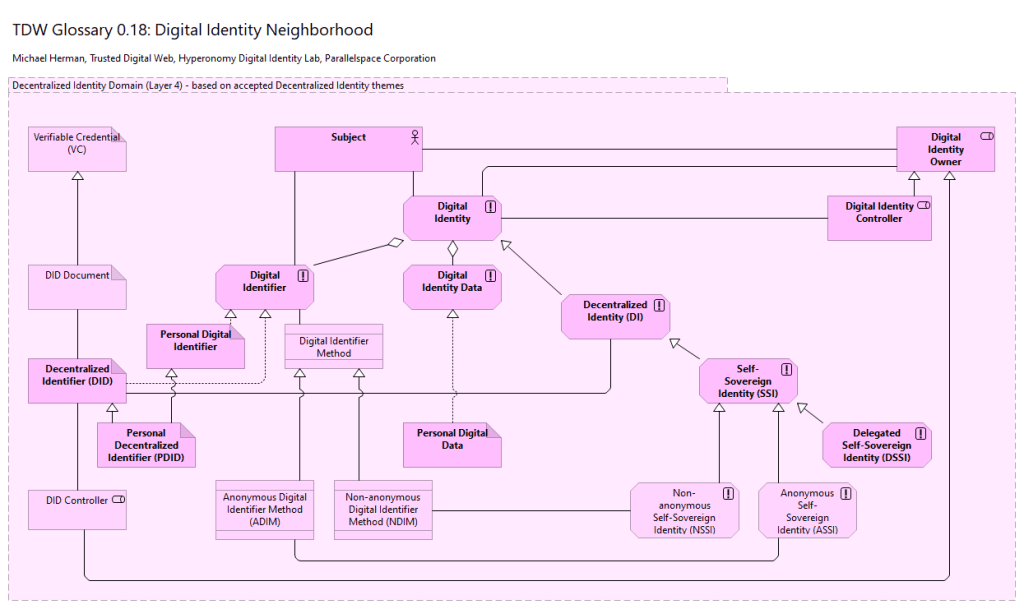
A Digital Identity aggregates:
A Decentralized Identity is a Digital Identity that is Verifiable.
A Decentralized Identity is often persisted in a Verifiable Data Register.
A Self-Sovereign Identity is a Digital Identity whose Digital Identity Owner has the right to exclusively and permanently exert control over the usage of one or more associated Personal Digital Identifiers and, independently, the usage of any associated Personal Identity Data associated with each Personal Digital Identifier.
Because a Self-Sovereign Identity is a specialization of Decentralized Identity, a Self-Sovereign Identity is also Verifiable.
A Digital Identity Owner is an entity that may be held legally accountable. Digital Identity Owners includes Persons and Organizations but does not include Things. The actual legal accountability of an Identity Owner for any particular action depends on many contextual factors including the laws of the applicable jurisdiction, etc. [Sovrin Glossary]
An Anonymous Self-Sovereign Identity is a Self-Sovereign Identity whose Personal Digital Identifier is associated with (or governed by) an Anonymous Digital Identifier Method.
A Non-anonymous Self-Sovereign Identity is a Self-Sovereign Identity whose Personal Digital Identifier is associated with (or governed by) a Non-anonymous Digital Identifier Method.
A Personal Digital Identifiers is a Digital Identifier associated with a Person as the Subject of the identifier.
Personal Digital Data is Digital Identity Data associated with a Personal Digital Identifier; and hence, a Person as the subject of the identifier.
An Anonymous Digital Identifier Method is a Digital Identifier Method designed to guarantee anonymity and privacy for the Subject of a conforming Digital Identifier.
A Non-anonymous Digital Identifier Method is a Digital Identifier Method that does not guarantee anonymity nor privacy for the Subject of a conforming Digital Identifier.
The next most commonly (and generically) used term is Self-Sovereign Identity Model (SSI Model).
The Self-Sovereign Identity Model (SSI Model) is an identity system architecture based on the core principle that Identity Owners have the right to permanently exert control over the usage of one or more of their Personal Digital Identifiers and, independently, the usage of any associated Personal Identity Data. [inspired by the Sovrin Glossary]
PLEASE POST A COMMENT ABOUT WHY THIS PAGE IS IMPORTANT TO YOU.
This particular page is 1 of my top 5 most viewed pages (ever) and I’d like to understand why. Thank you!
Click here to download the whitepaper:
Filed under Uncategorized
Copyright (c) 2019 Michael Herman (Alberta, Canada) – Creative Commons Attribution-ShareAlike 4.0 International Public License
https://creativecommons.org/licenses/by-sa/4.0/legalcode
Ahead of schedule, the first trusted web page was delivered today on the Trusted Digital Web – end-to-end – from a Trusted Digital Web – Data Registry service to a Trusted Digital Assistant client application – using didttp: (DID Trusted Transport Protocol).
The Trusted Digital Web Communication Protocols (include ddttp:) are described in Appendix E of the Trusted Digital Web: Whitepaper.
NOTE: The Trusted Digital Web is built on top of and relies on trusted, everyday Internet protocols, services, and specifications such as DNS (Domain Name Service). If you’re unfamiliar with DNS at a technical level, checkout DNS (Domain Name Service): A Detailed, High-level Overview.
NOTE: The UDID Data Registry is a fork of DNS Server (https://github.com/TechnitiumSoftware/DNSServer). Thank you Shreyas Zare.
Here’s some screenshots to document this significant event.
The DIDTXT claim will hold the contents of the index.html web page.
Navigate to a conventional web page (e.g. http://www.hyperonomy.com).
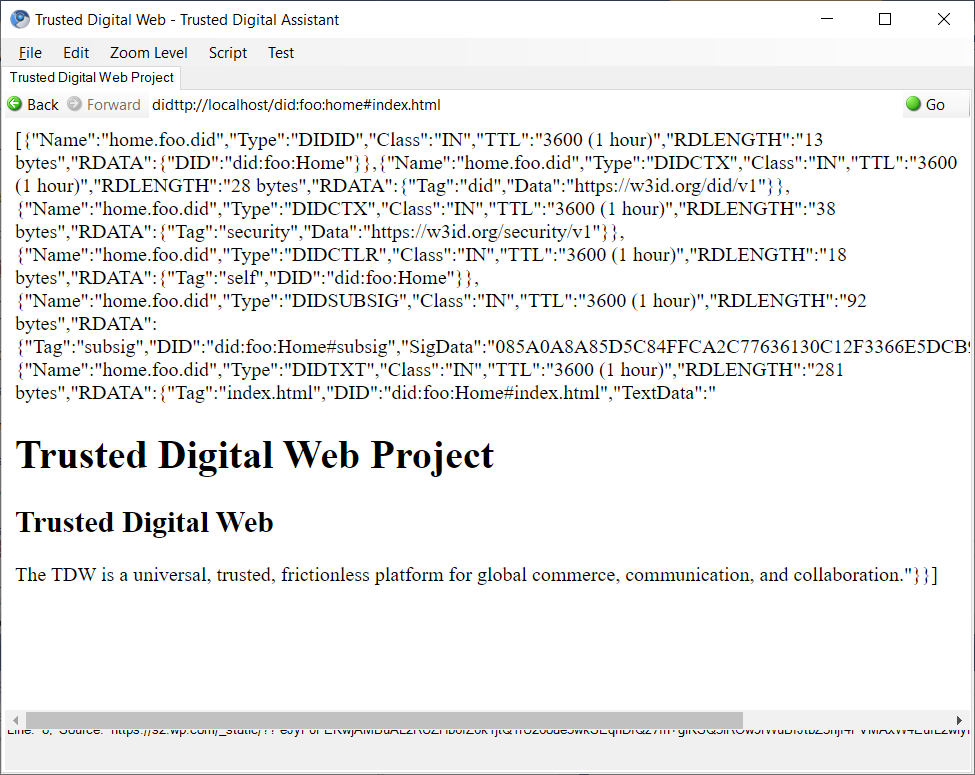
Voila.
To learn more about the Trusted Digital Web project, checkout Trusted Digital Web: Whitepaper.
Filed under Uncategorized
From the Trusted Digital Web whitepaper…
For a deeper understanding of Universal Digital Identifiers, Universal Digital Identities, and the Trusted Digital Web, checkout the Trusted Digital Web: Whitepaper.
Filed under TDW, Trusted Digital Web
Two of the key concepts in the Trusted Digital Web are:
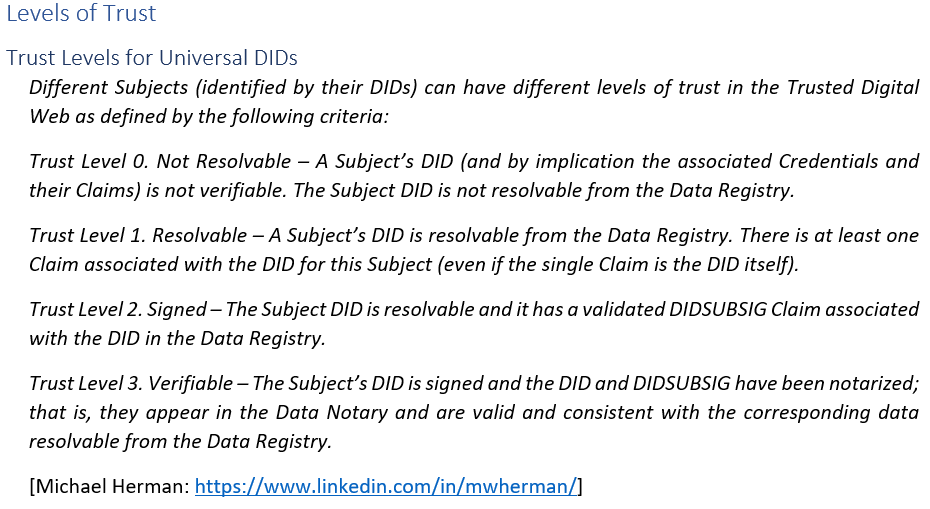

For a deeper understanding of Universal Digital Identifiers, Universal Digital Identities, and the Trusted Digital Web, checkout the Trusted Digital Web: Whitepaper.
Filed under TDW, Trusted Digital Web
Copyright (c) 2019 Michael Herman (Alberta, Canada) – Creative Commons Attribution-ShareAlike 4.0 International Public License
https://creativecommons.org/licenses/by-sa/4.0/legalcode
Click here to download the whitepaper:
NOTE: The glossaries can be found in Appendices B and C and D of the whitepaper.
Click here for a video introduction to the Trusted Digital Web (first 3 videos).
Filed under TDW, Trusted Digital Web
Click here (to download the whitepaper): Trusted Digital Web: Whitepaper [Preview Draft] (PDF).
The current version of the glossaries can be found in Appendices B and C.
Filed under TDW, Trusted Digital Web