Create your own magic with Web 7.0™ / TDW AgenticOS™. Imagine the possibilities.
Copyright © 2019-2025 Michael Herman (Bindloss, Alberta, Canada) – Creative Commons Attribution-ShareAlike 4.0 International Public License
Web 7.0™, TDW AgenticOS™ and Hyperonomy™ are trademarks of the Web 7.0 Foundation. All Rights Reserved.
[Original Title: Technology Adoption Models: A Comprehensive Guide]
This article documents more than 20 technology adoption models that the author has encountered over his 45+ year career …some models that he didn’t even realize he knew about ;-). Here they there are, in no particular order.
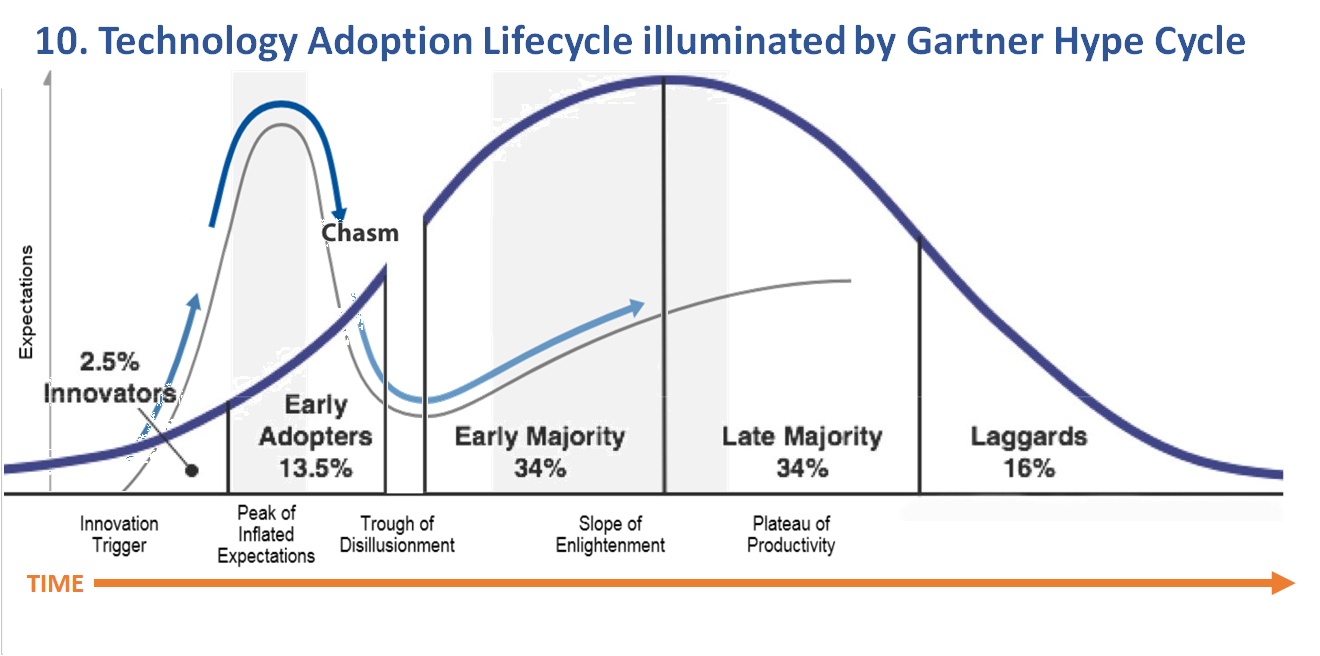
NOTE: Each model progresses from left-to-right along an unspecified timeline. The implication is that it is possible to superimpose two or more models on top of each other for deeper understanding and for creating more tangible, more illustrative, depictions of your corporate, product, and project strategies.
An example is: Model 10. Technology Adoption Lifecycle illuminated by the Gartner Hype Cycle.
Technology Adoption Models
NOTE: Click on any of the figures to enlarge them.
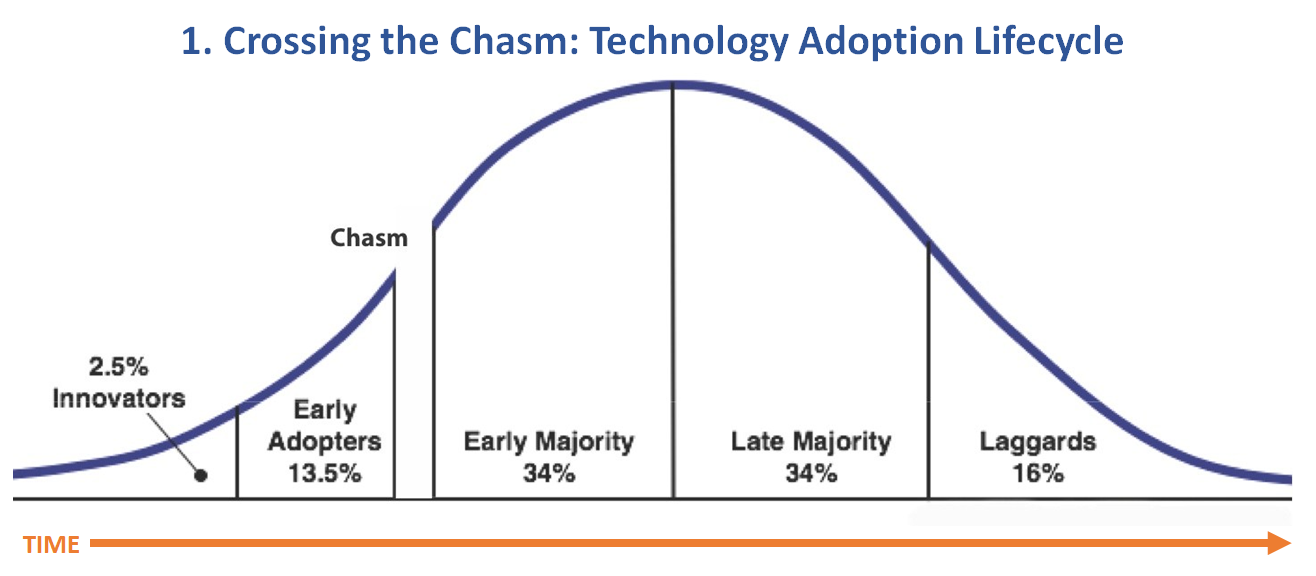
Model 1. Crossing the Chasm: Technology Adoption Lifecycle
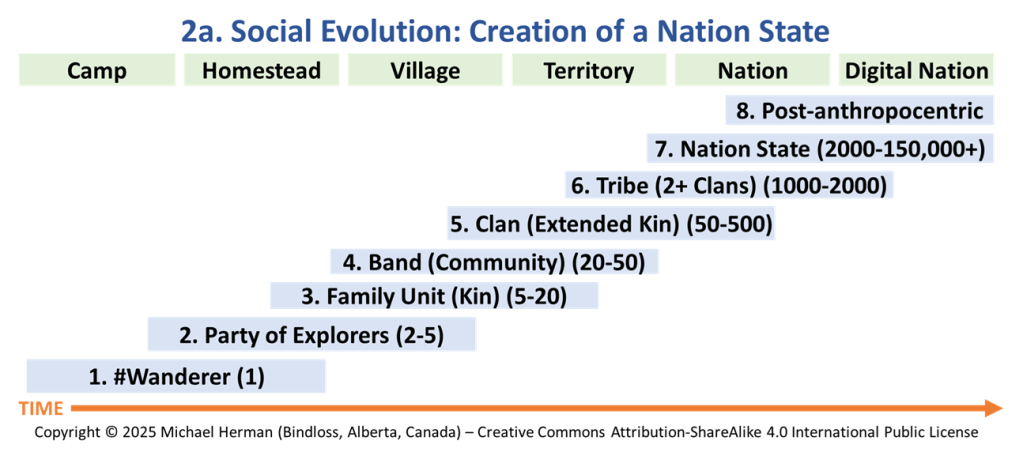
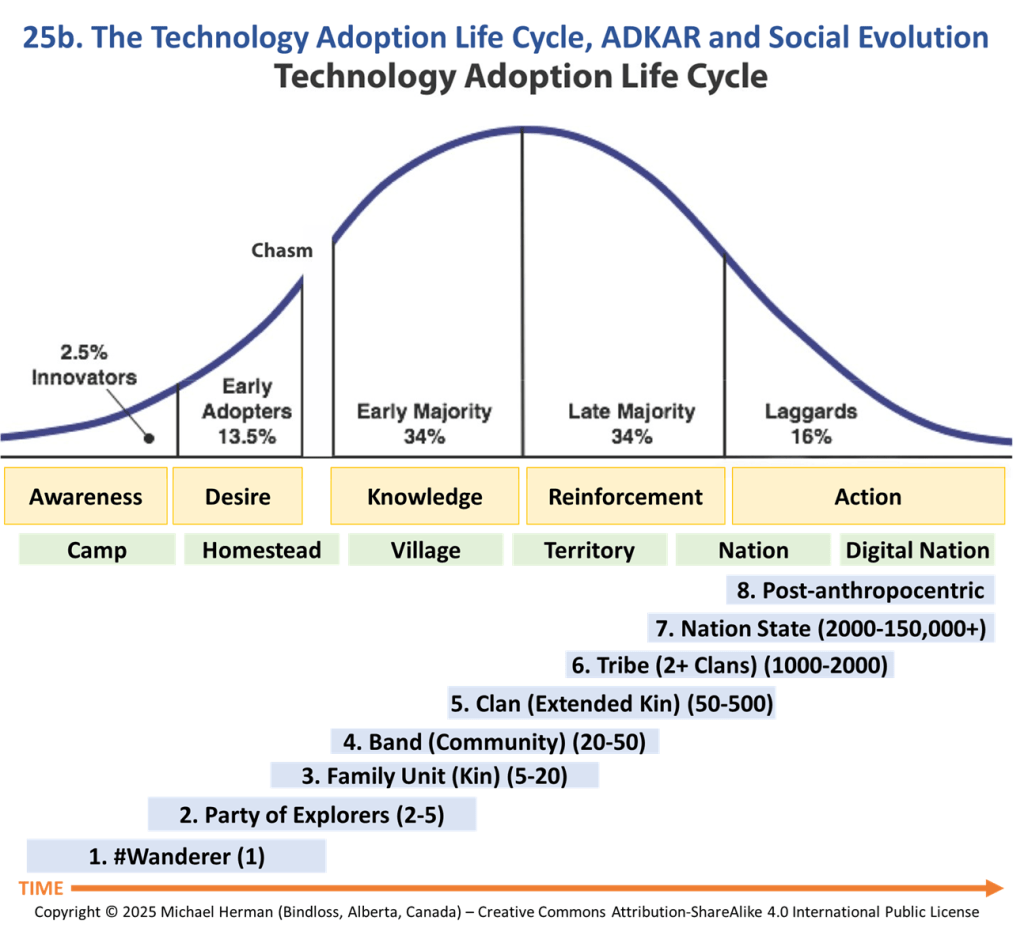
Model 2a. Social Evolution: Creation of Nation State
A #wanderer is someone who leaves their tribe to share their knowledge and wisdom with others; to later form a party of explorers to explore and conquer a common set of goals; and, even further on, create a clan, a band, a tribe, and a tribal society, a group of people who live and work together – a group of tribes organized around kinships.
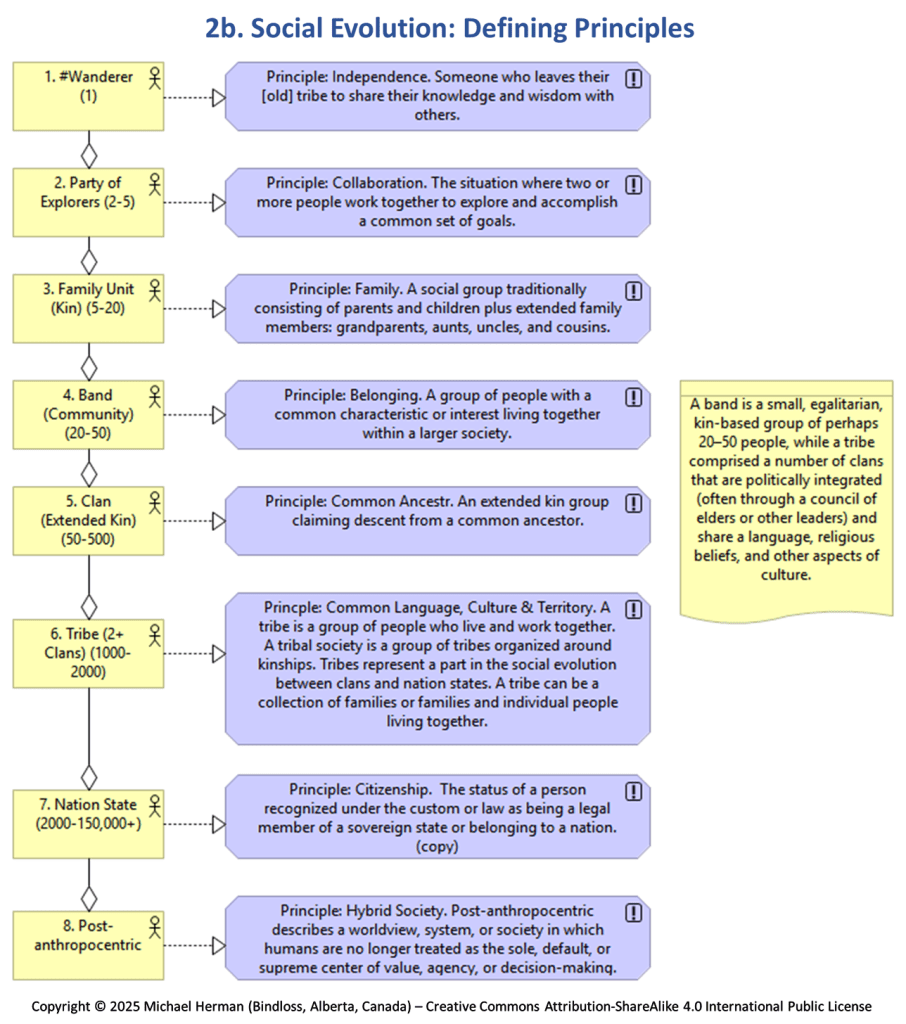
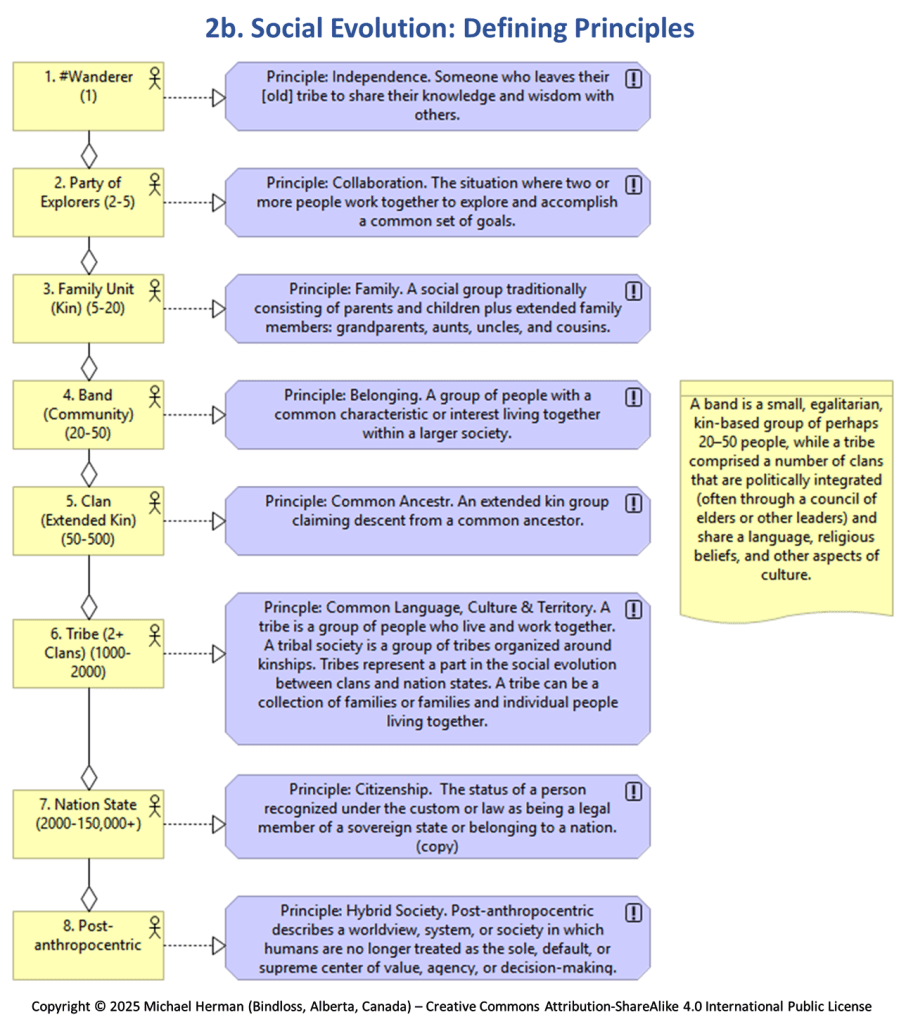
Model 2b. Social Evolution: Defining Principles
A #wanderer is someone who leaves their tribe to share their knowledge and wisdom with others; to later form a party of explorers to explore and conquer a common set of goals; and, even further on, create a clan, a band, a tribe, and a tribal society, a group of people who live and work together – a group of tribes organized around kinships.
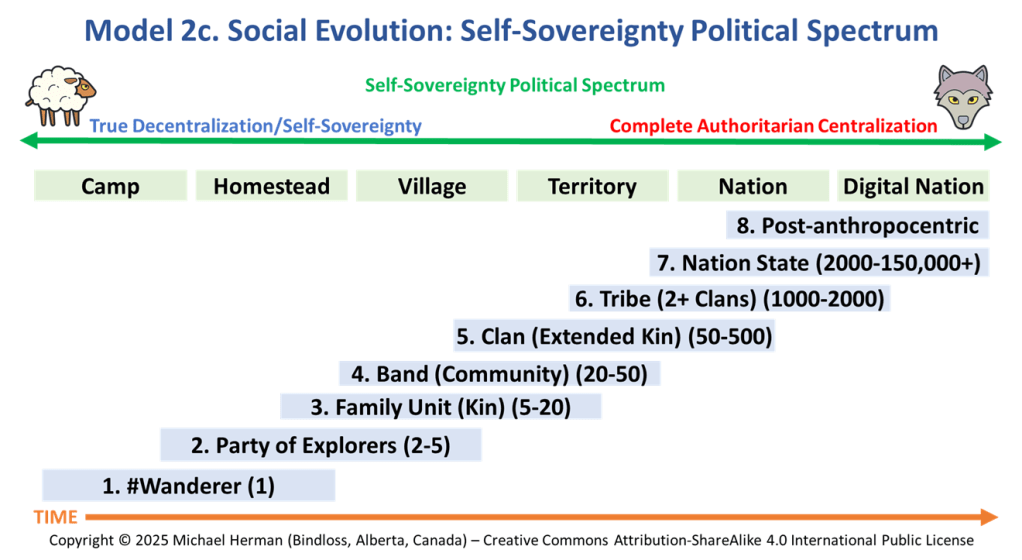
Model 2c. Social Evolution: Self-Sovereignty Political Spectrum
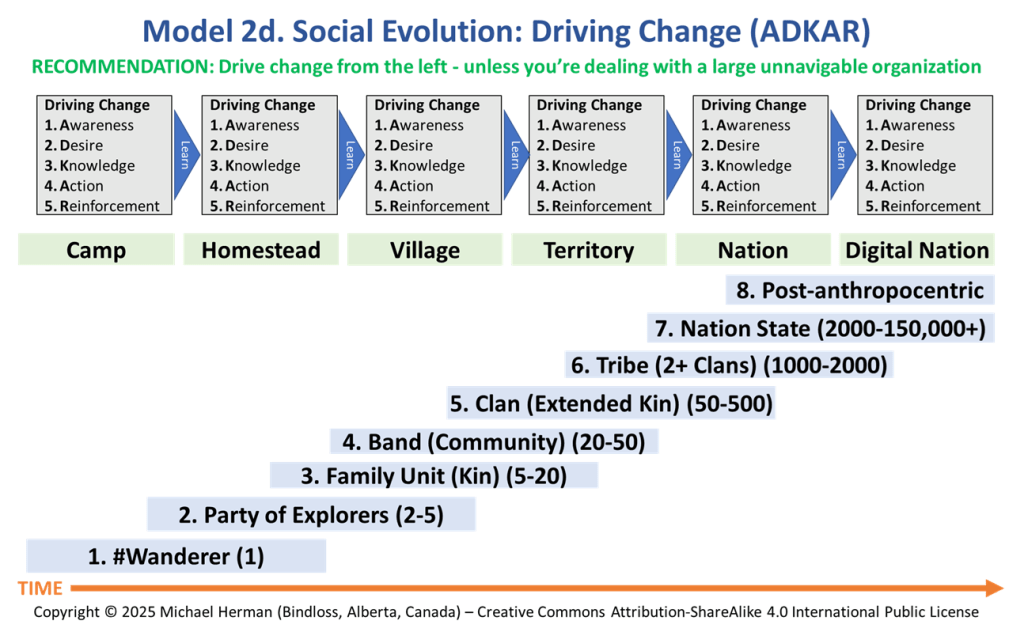
Model 2d. Social Evolution: Driving Change (ADKAR)
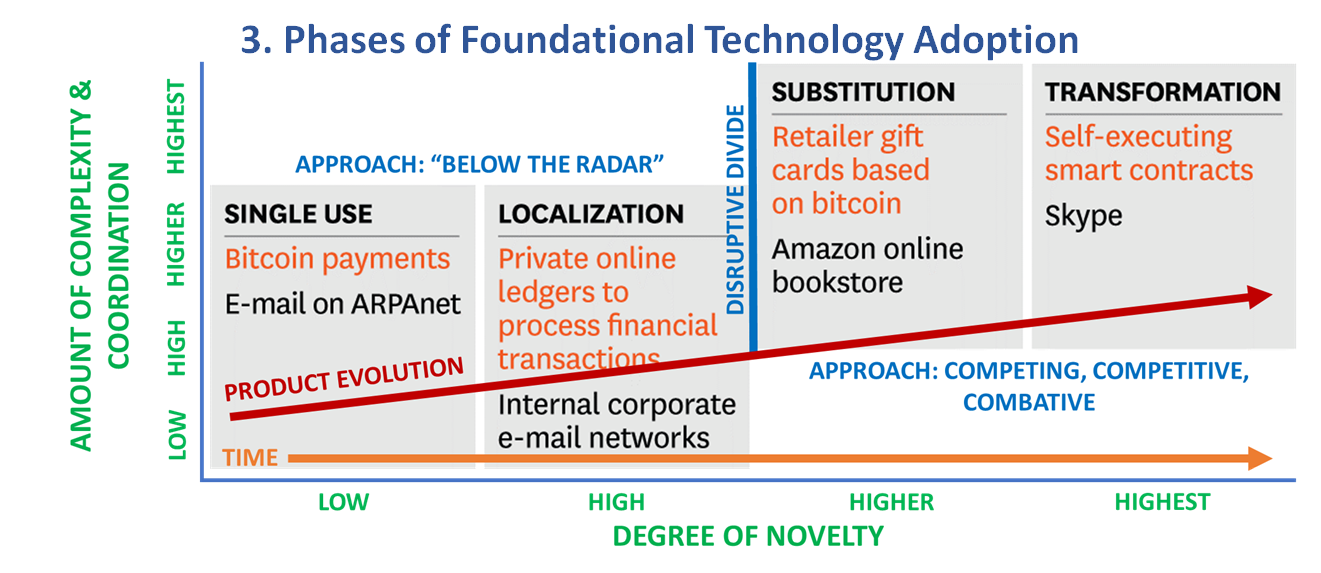
Model 3. Phases of Foundational Technology Adoption
Model 4. Phases of Desire and Action
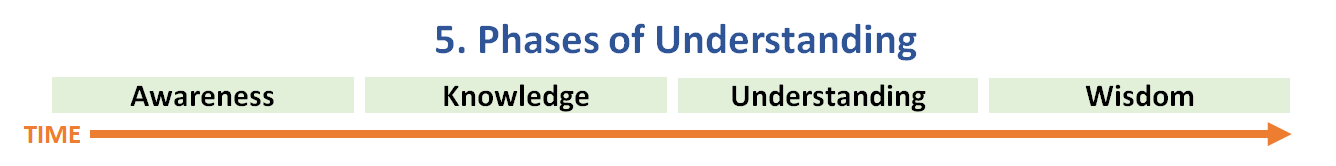
Model 5. Phases of Understanding
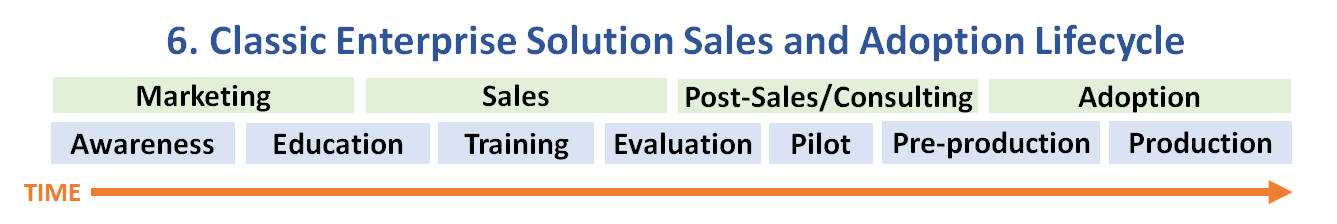
Model 6. Classic Enterprise Solution Sales and Adoption Lifecycle
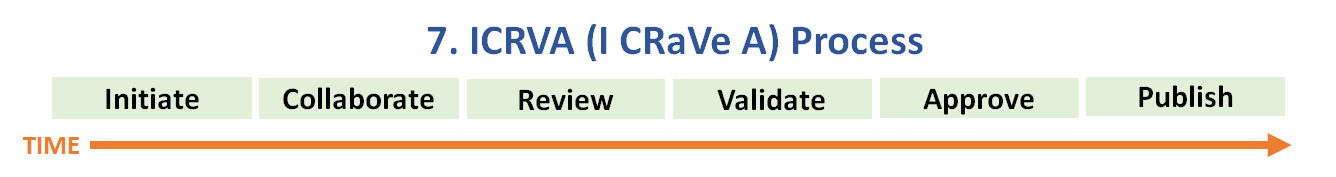
Model 7. ICRVA (I CRaVe A) Process
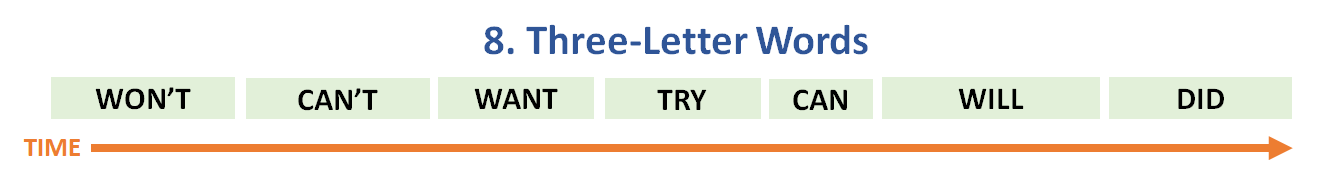
Model 8. Three-letter Words
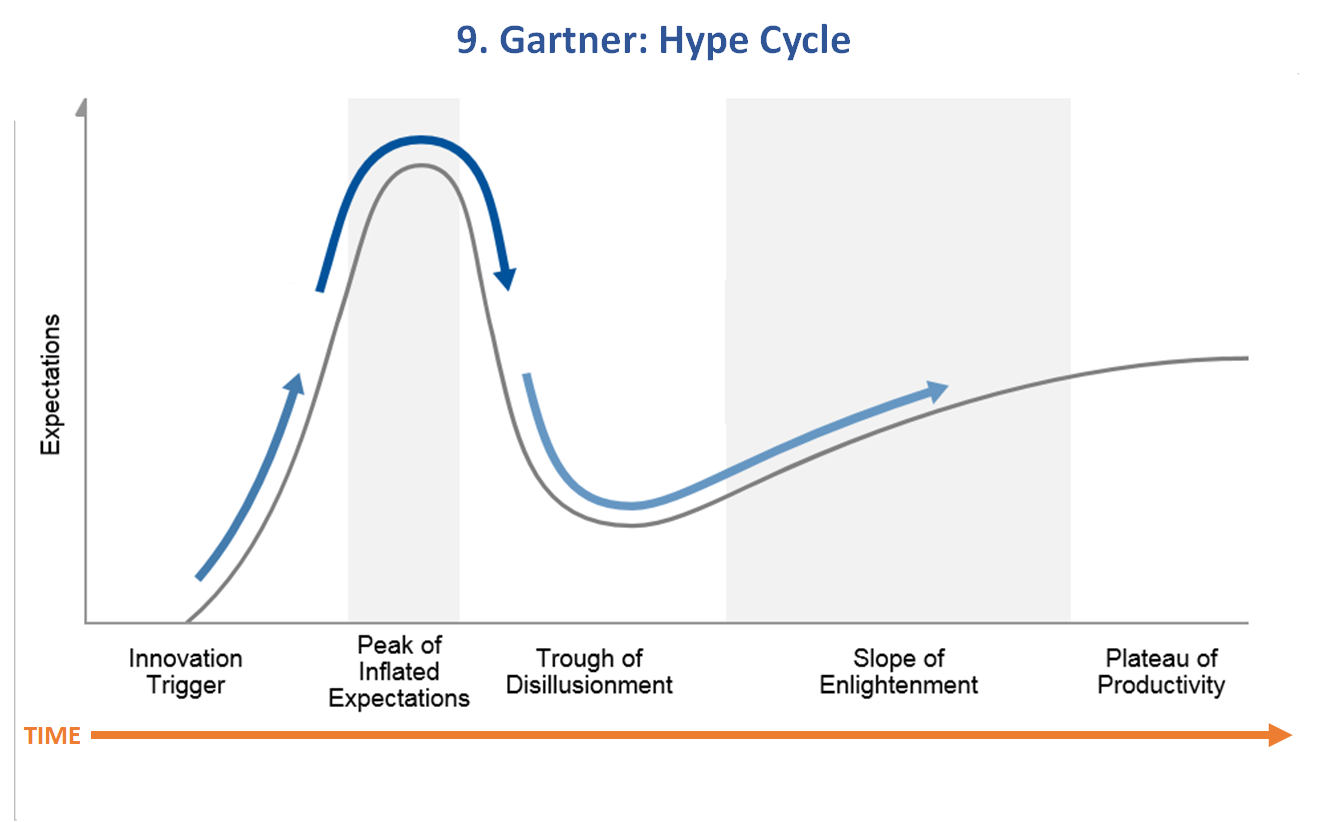
Model 9. Gartner Hype Cycle
Model 10. Technology Adoption Lifecycle illuminated by the Gartner Hype Cycle
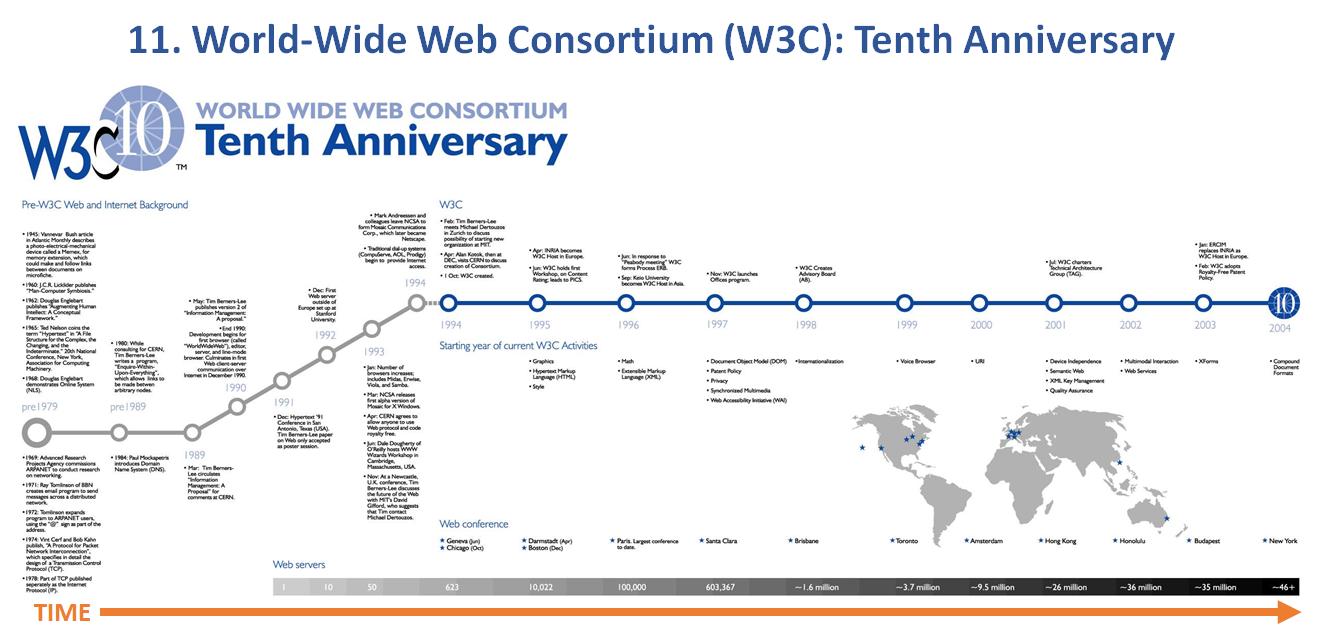
Model 11. World Wide Web Consortium (W3C): Tenth Anniversary
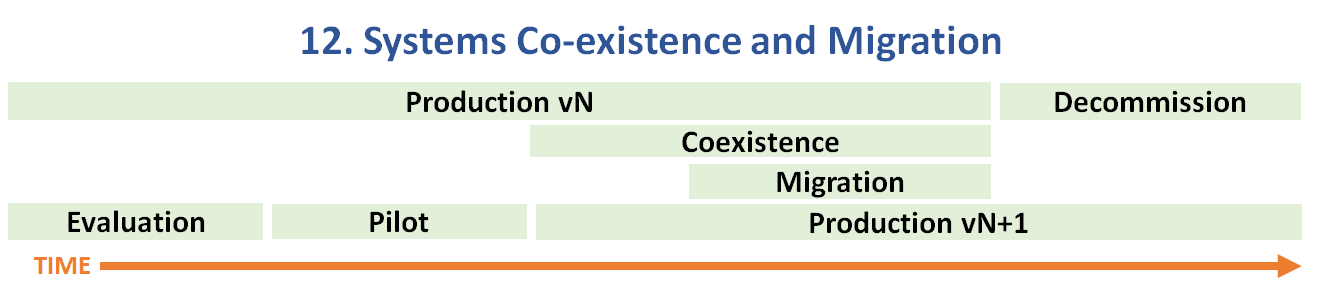
Model 12. Systems Co-existence and Migration
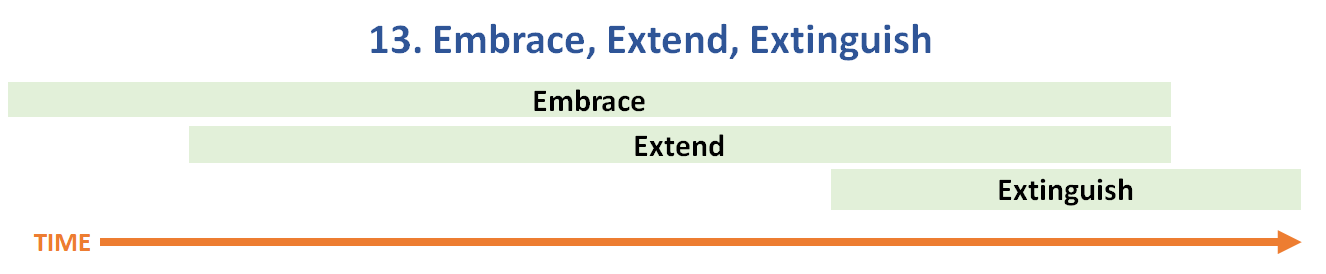
Model 13. Embrace, Extend, and Extinguish
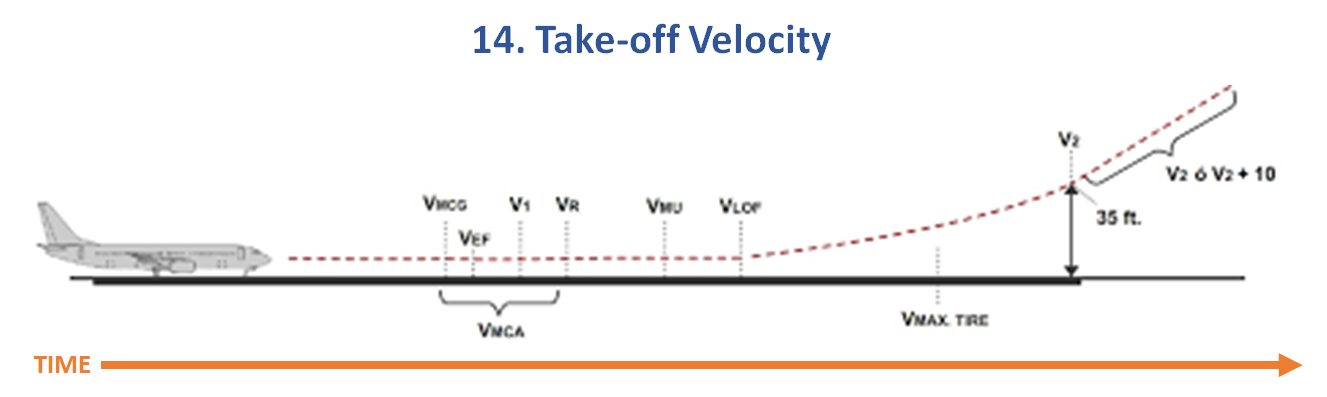
Model 14. Take-off Velocity (v2)
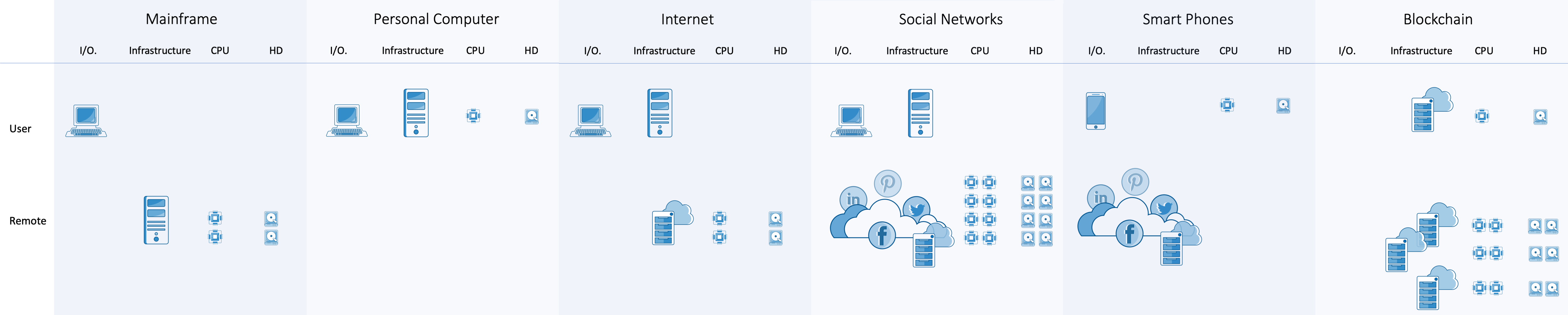
Model 15. From Mainframe to Blockchain

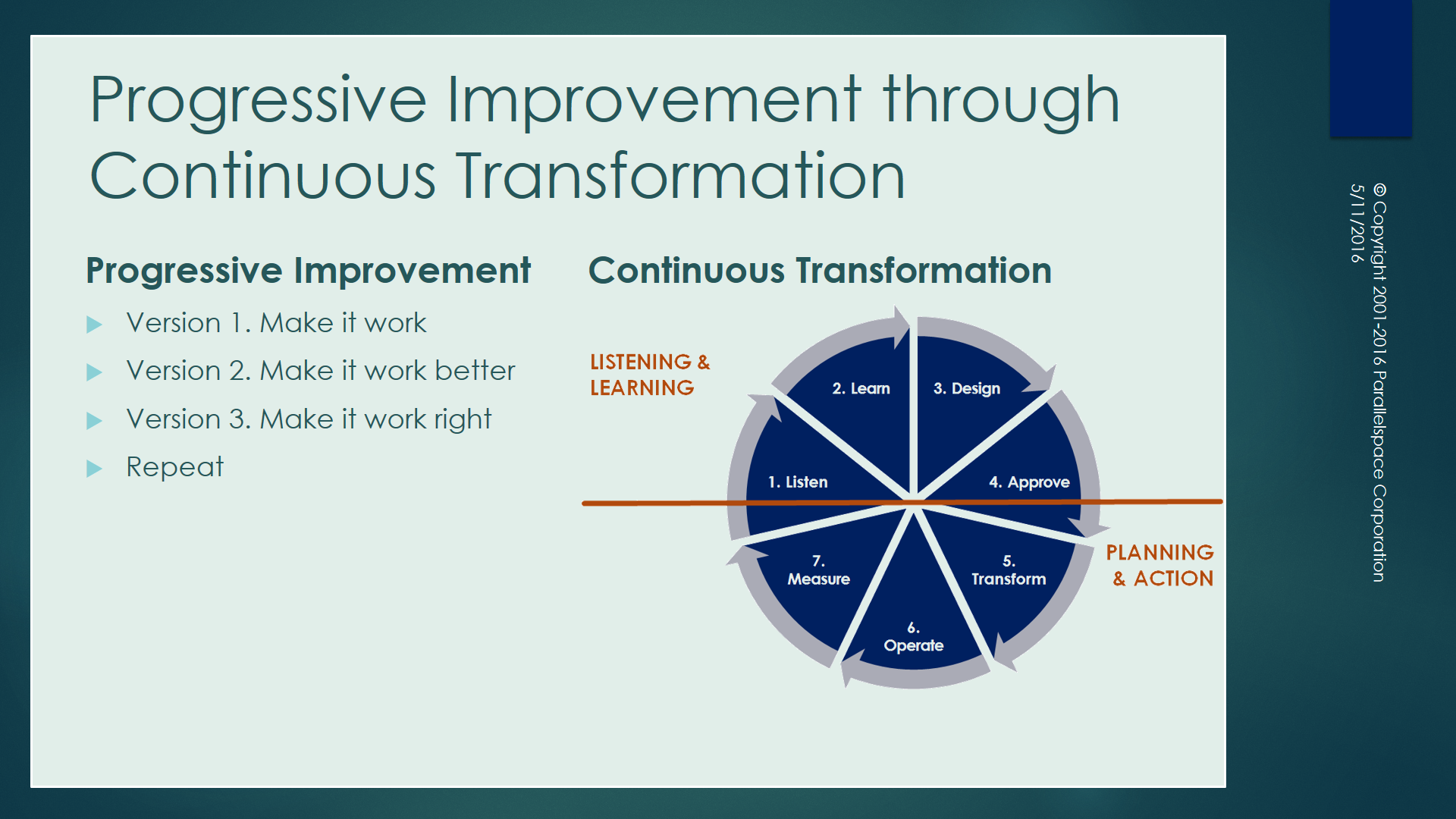
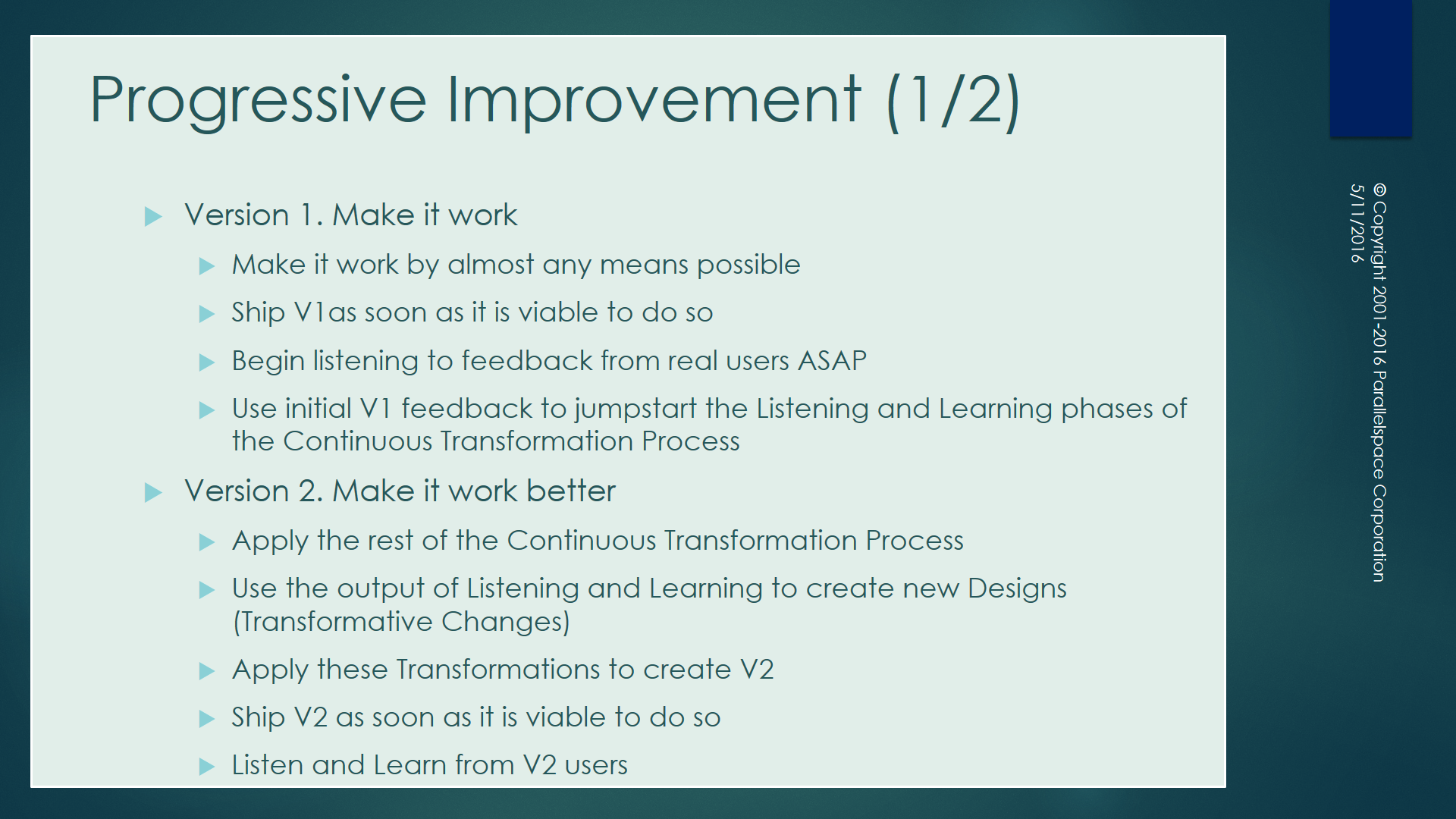
Model 16. Progressive Improvement through Continuous Transformation

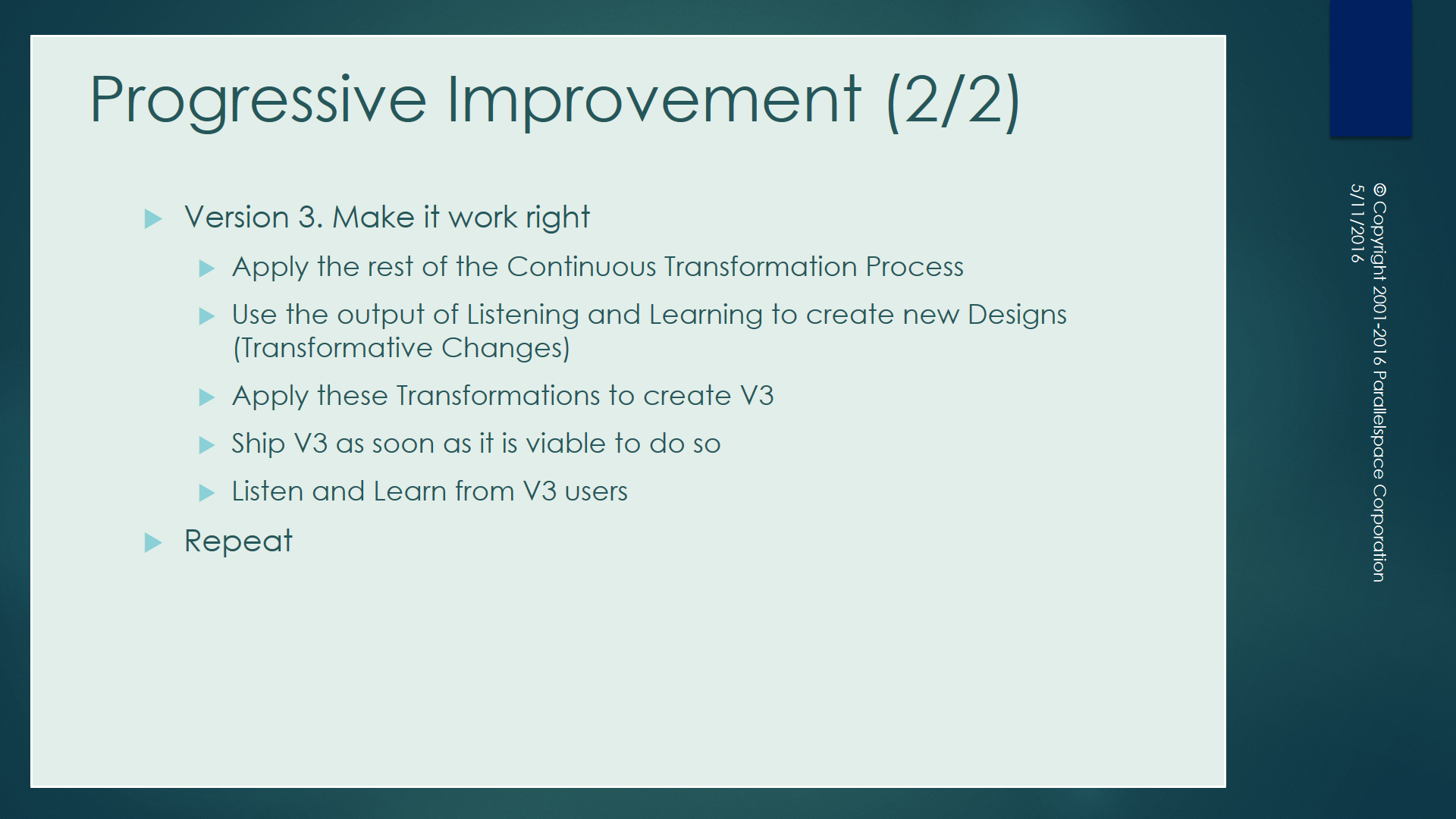
Model 17. Liedtka-Ogilvie Design Thinking Model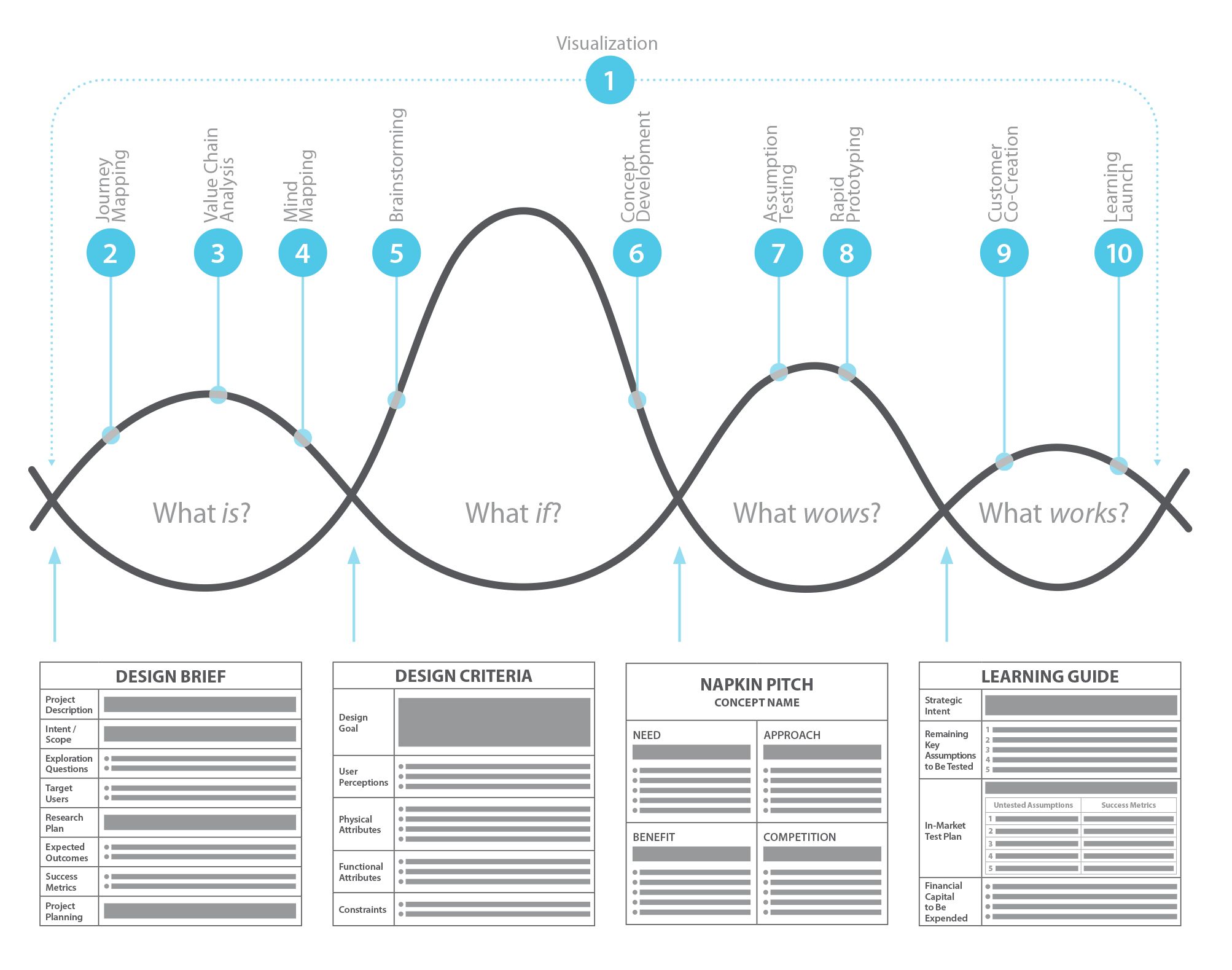 Model 18. CB-Insights NExTT Framework
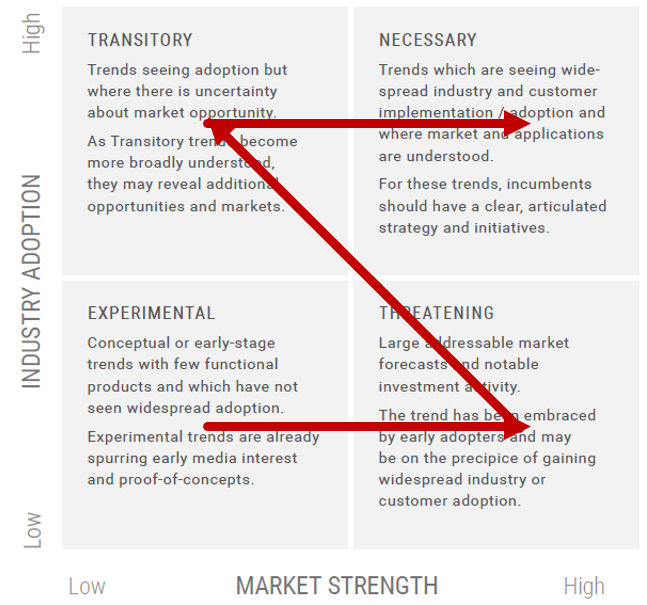
Model 18. CB-Insights NExTT Framework
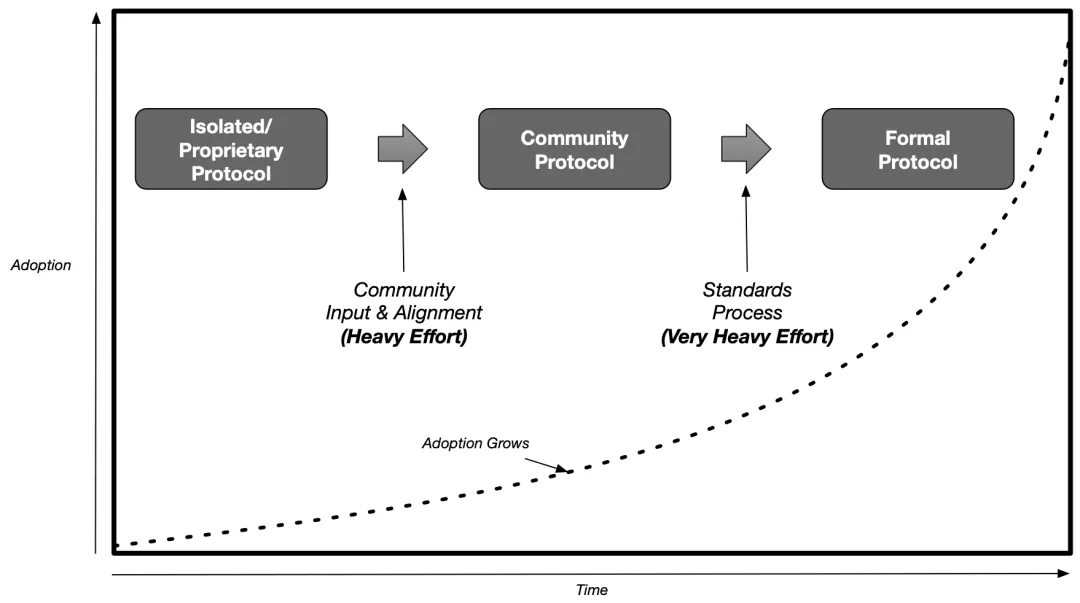
Model 19. O’Donnell Exponential Growth Model
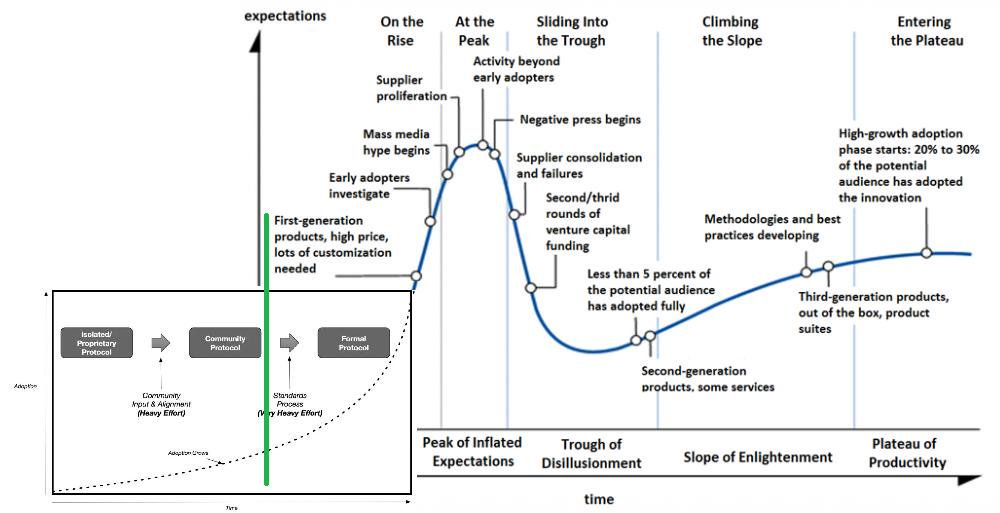
Model 20. O’Donnell-Gartner Exponential Hype Cycle
Model 21. Technical Intensity (video)

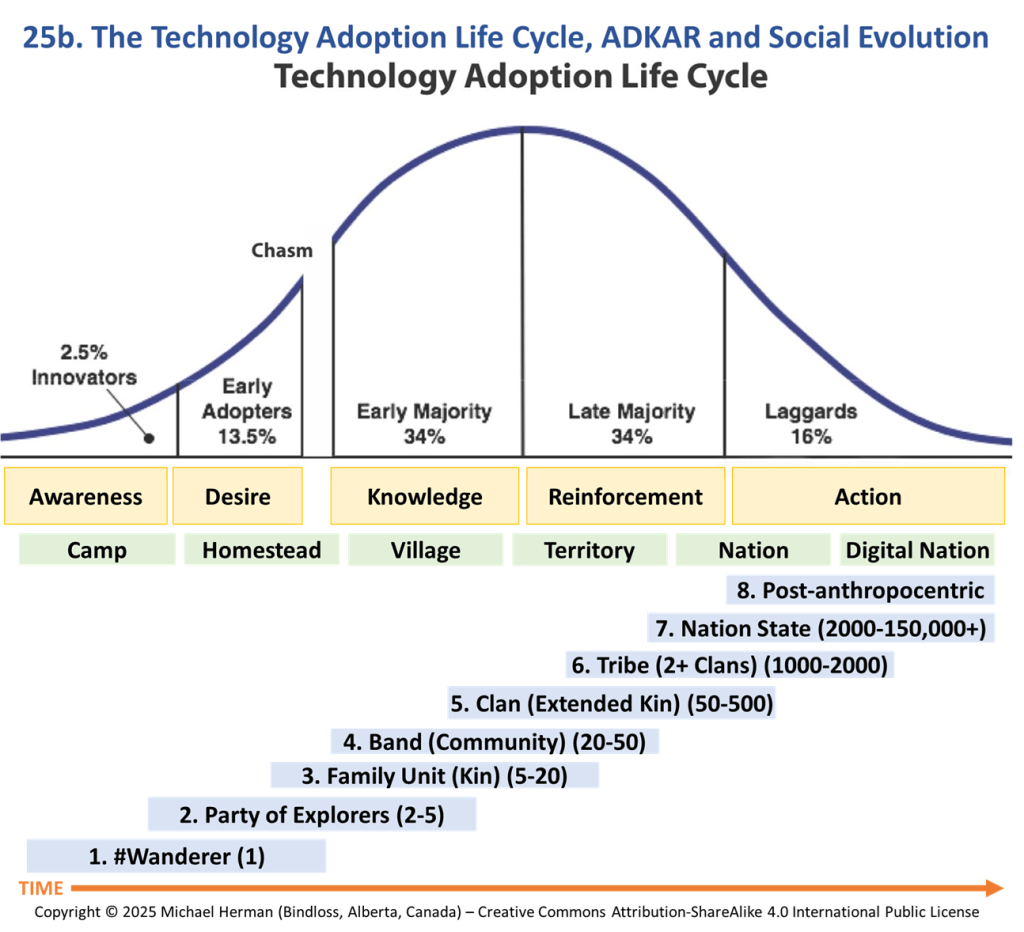
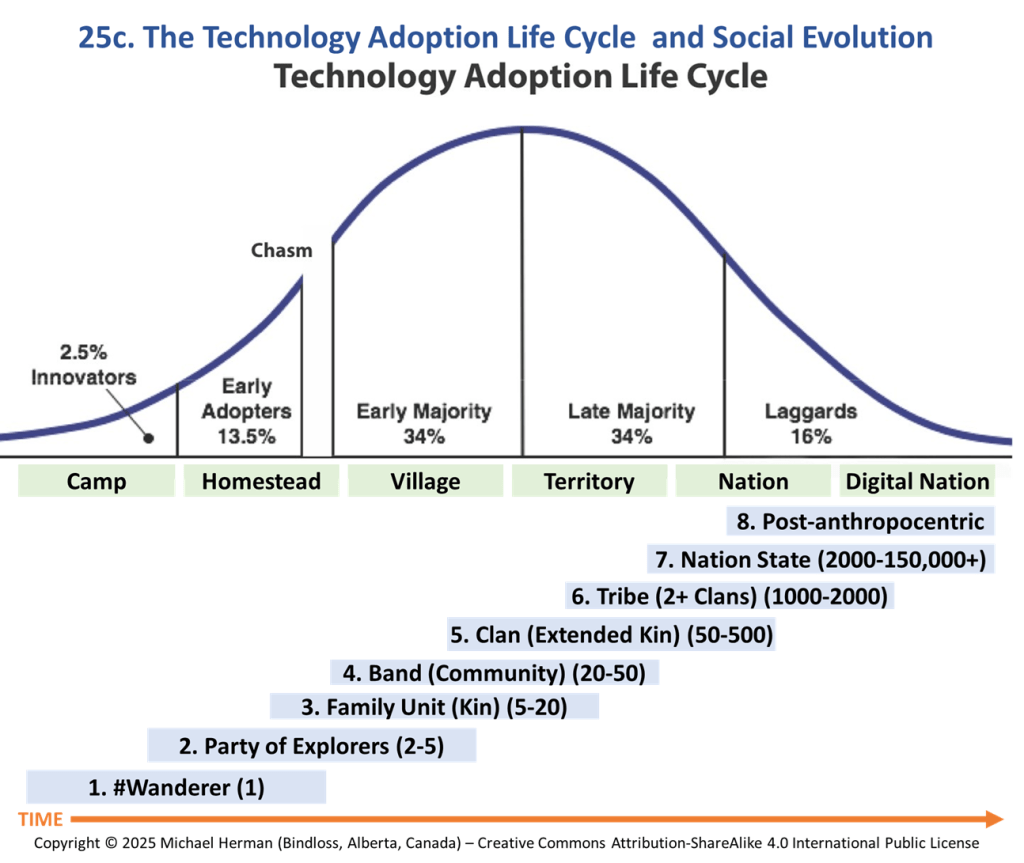
Model 22. Technology Adoption Curve plus Social Evolution Model
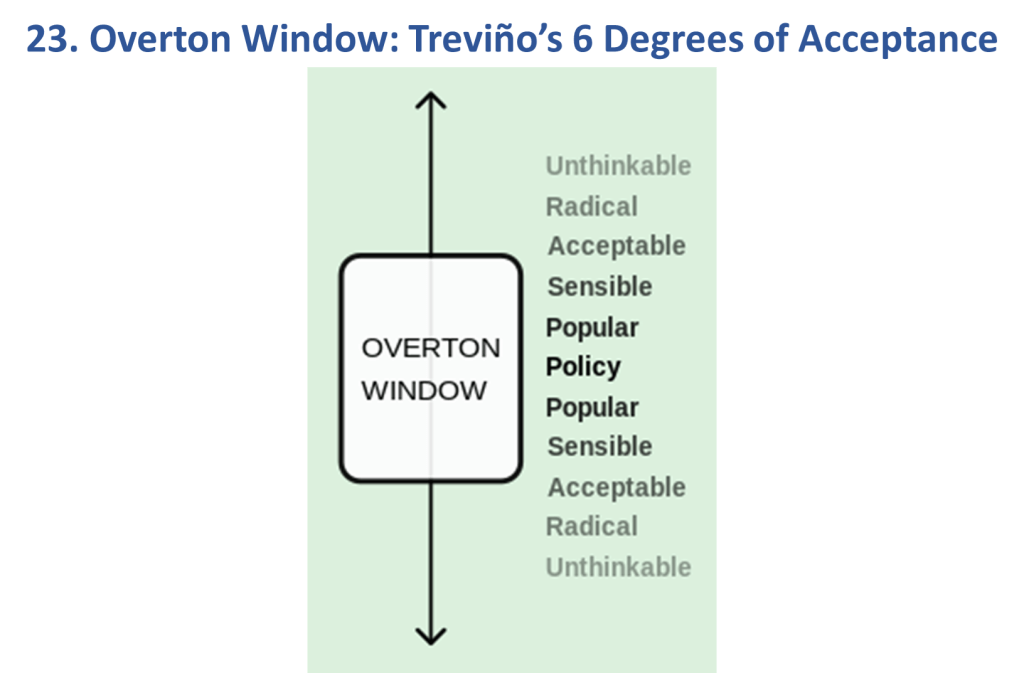
Model 23: Overton Window
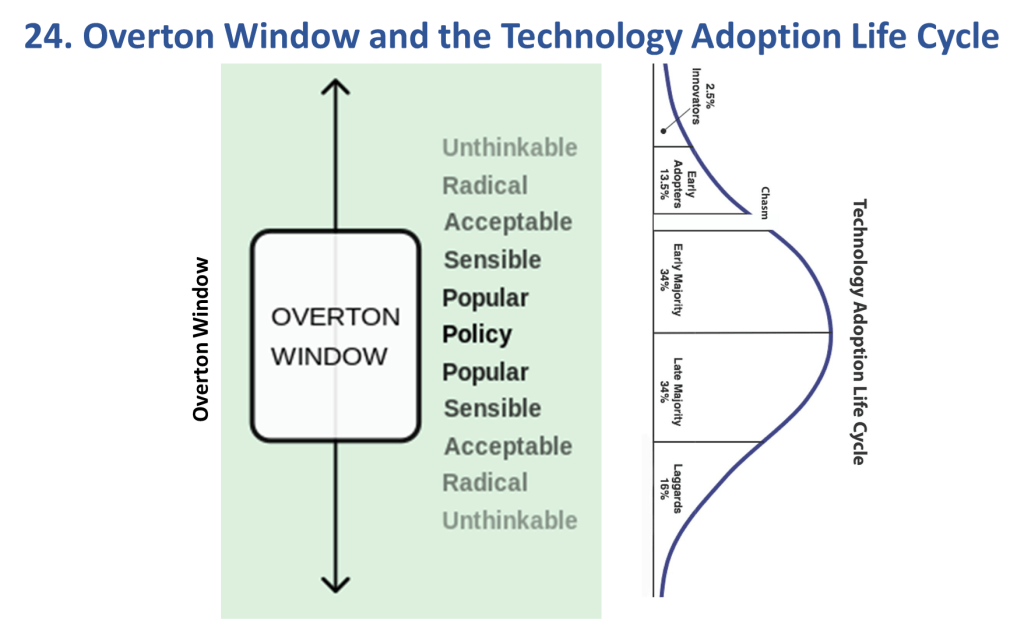
Model 24: Overton Window and Technology Adoption Lifecycle
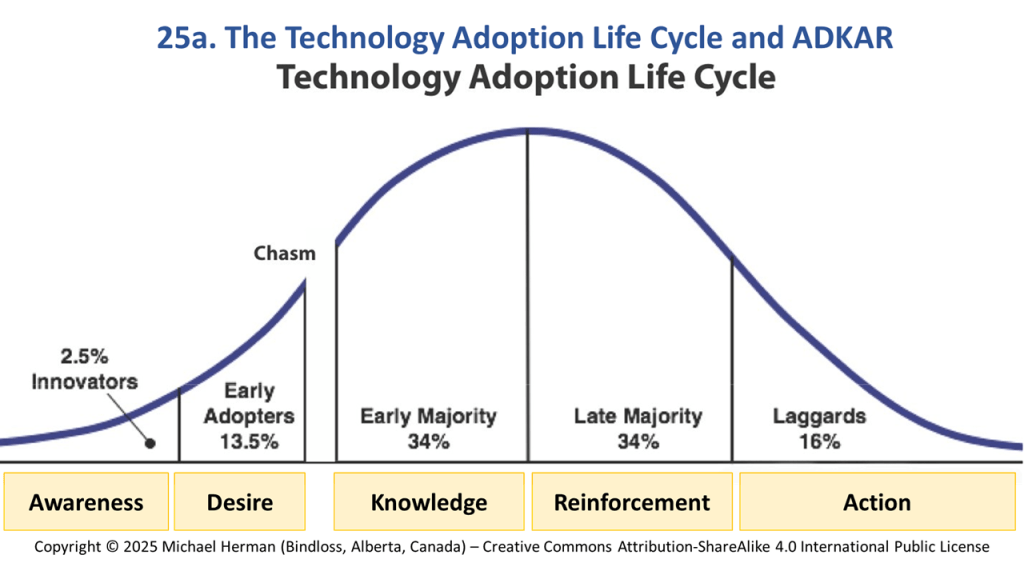
Model 25: The Technology Adoption Lifecycle and ADKAR
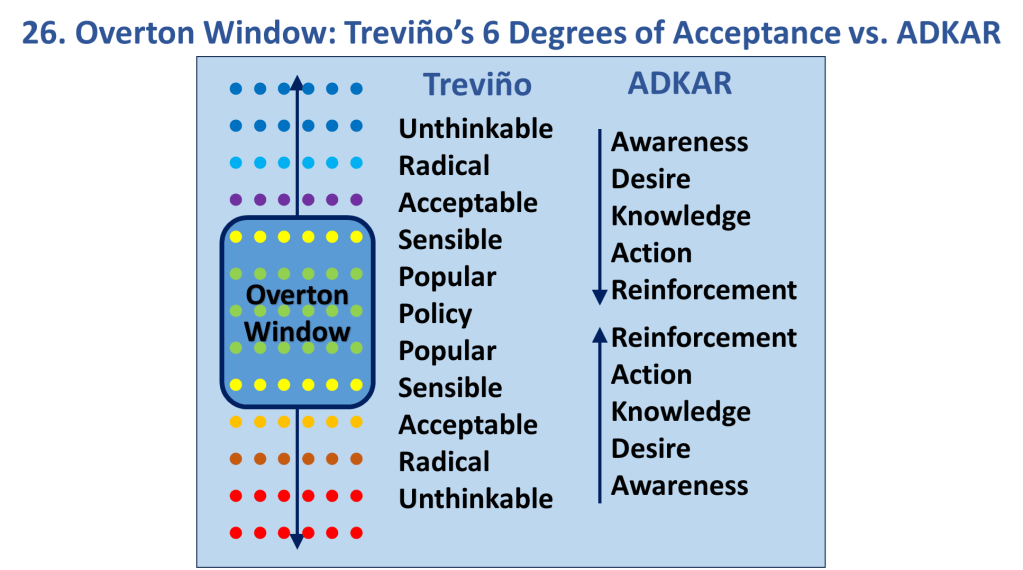
Model 26: Overton Window: Treviño’s 6 Degrees of Acceptance vs. ADKAR
References
[Model 1] Crossing the Chasm: Marketing and Selling High-Tech Products to Mainstream Customers (https://en.wikipedia.org/wiki/Crossing_the_Chasm)
[Model 2a] Michael Herman (https://www.linkedin.com/in/mwherman/)
[Model 2b] Michael Herman (https://www.linkedin.com/in/mwherman/)
[Model 2c] Michael Herman (https://www.linkedin.com/in/mwherman/)
[Model 2d] Michael Herman (https://www.linkedin.com/in/mwherman/) and ADKAR Change Management Model (https://www.prosci.com/adkar/adkar-model_
[Model 3] Phases of Foundational Technology Adoption (https://www.linkedin.com/pulse/blockchain-foundational-technology-michael-herman/)
[Model 4] Michael Herman (https://www.linkedin.com/in/mwherman/)
[Model 5] Michael Herman (https://www.linkedin.com/in/mwherman/)
[Model 6] Michael Herman (https://www.linkedin.com/in/mwherman/)
[Model 7] How We Think About How We Work (https://hyperonomy.com/2016/05/09/how-do-we-think-about-how-we-work/)
[Model 8] Unknown (with apologizes from the author)
[Model 9] Gartner Hype Cycle (https://www.gartner.com/en/research/methodologies/gartner-hype-cycle)
[Model 10] Gartner Hype Cycle (https://www.gartner.com/en/research/methodologies/gartner-hype-cycle) and Michael Herman (https://www.linkedin.com/in/mwherman/)
[Model 11] World Wide Web Consortium (W3C): Timeline Graphic (https://www.w3.org/2005/01/timelines/description)
[Model 12] Microsoft Corporation (https://en.wikipedia.org/wiki/Embrace,_extend,_and_extinguish)
[Model 13] Unknown (with apologizes from the author)
[Model 14] Unknown (with apologizes from the author)
[Model 15] Medium.com: From mainframes to blockchains. How to look at the future. (https://medium.com/@ben_longstaff/my-framework-for-how-to-look-at-the-future-of-blockchain-719f4243491f)
[Model 16] How We Think About How We Work (https://hyperonomy.com/2016/05/09/how-do-we-think-about-how-we-work/)
[Model 17] Designing for Growth: A Design Thinking Tool Kit for Managers (http://www.designingforgrowthbook.com/)
[Model 18] CB-Insights NExTT Framework (https://www.cbinsights.com/)
[Model 19 and 20] Darrell O’Donnell. The Current and Future State of Digital Wallets (https://www.continuumloop.com/standards-digitalwallet-part-11-16/).
[Model 20] Gartner Hype Cycle (https://www.gartner.com/en/research/methodologies/gartner-hype-cycle) and Michael Herman (https://www.linkedin.com/in/mwherman/)
[Model 21] Vision Keynote with Satya Nadella | Microsoft Ignite 2019 (https://www.youtube.com/watch?v=jnUiJi4hts4)
[Model 22] Michael Herman (https://www.linkedin.com/in/mwherman/)
[Model 23] Overton Window (https://en.wikipedia.org/wiki/Overton_window)
[Model 24] Michael Herman (https://www.linkedin.com/in/mwherman/)
[Model 25] Michael Herman (https://www.linkedin.com/in/mwherman/)
[Model 26] Michael Herman (https://www.linkedin.com/in/mwherman/)
Resources
- Phases of Foundational Technology Adoption (https://www.linkedin.com/pulse/blockchain-foundational-technology-michael-herman/)