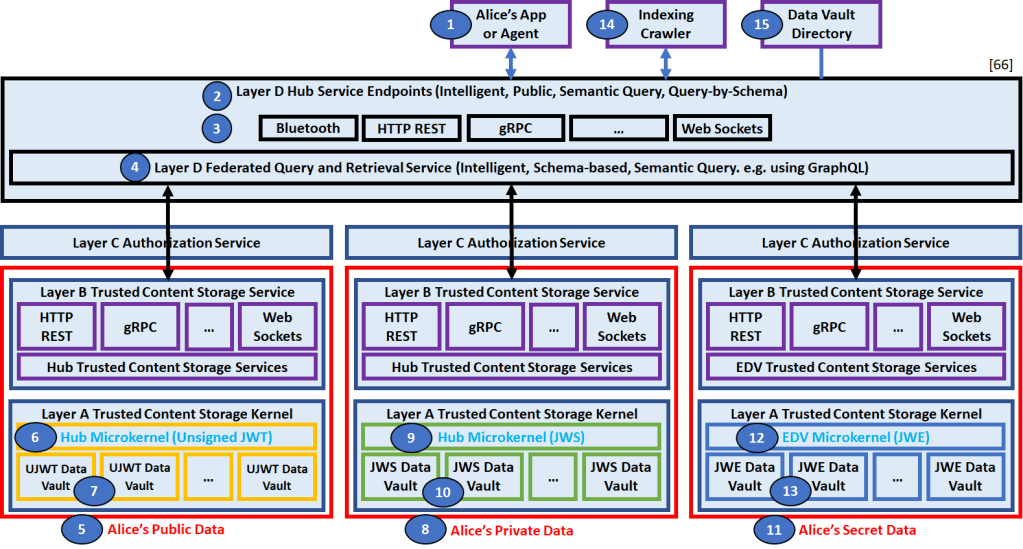
Click the HUB-ARM to enlarge it. It will open in a new tab. Read the narration provided below the HUB-ARM.
Narration
Each bullet in the list below describes a numbered bubble in the diagram above.
- Alice’s App (1) has secure access to Alice’s Public Data (5), Alice’s Private Data (8), and Alice’s Secret Data (11).
- Alice’s App (1)’s secure access is realized by the Layer D Hub Service Endpoints (2). The Layer D Hub Service Endpoints (2) support intelligent, semantics-based, query-by-schema access via a pubic interface exposed by a collection of Hub Protocol Handlers (3).
- Layer D Hub Service Endpoints (2)’s collection of supported Hub Protocol Handlers (3) might include: Bluetooth, HTTP REST, gRPC, Web Sockets, etc.
- Layer D Hub Service Endpoints (2) primarily provide access to the functionality supported by the Layer D Federated Query and Retrieval Service (4). The functionality supported by the Layer D Federated Query and Retrieval Service includes intelligent federated routing of semantics and schema-based queries plus aggregated retrieval of matching resources from Alice’s Public Data (5), Alice’s Private Data (8), and/or Alice’s Secret Data (11).
- Alice’s Public Data (5) is managed by the Hub Microkernel (6) which supports UJWT Data Vaults (7) containing collections of unsigned JWT resources.
- The Hub Microkernel (6) provides CRUD access to the collections of unsigned JWT resources in one or more UJWT Data Vaults (7) attached to the Hub Microkernel (6).
- One or more UJWT Data Vaults (7) can be attached to a Hub Microkernel (6) and are used to store collections of unsigned JWT resources.
- Alice’s Private Data (8) is managed by the Hub Microkernel (9) which supports JWS Data Vaults (10) containing collections of JWS (signed JWT) resources.
- The Hub Microkernel (9) provides CRUD access to the collections of JWS (signed JWT) resources in one or more JWS Data Vaults (10) attached to the Hub Microkernel (9).
- One or more JWS Data Vaults (10) can be attached to a Hub Microkernel (9) and are used to store collections of JWS (signed JWT) resources.
- Alice’s Secret Data (11) is managed by the EDV Microkernel (12) which supports JWE Data Vaults (13) containing collections of JWE (encrypted JWT) resources.
- The EDV Microkernel (12) provides CRUD access to the collections of JWE (encrypted JWT) resources in one or more JWE Data Vaults (13) attached to the EDV Microkernel (12).
- One or more JWE Data Vaults (13) can be attached to an EDV Microkernel (12) and are used to store collections of JWE (encrypted JWT) resources.
- An Indexing Crawler Service (14) might enable the indexing of publicly available content in Alice’s Data Vaults (7, 10, 13). Private and Secret Data Vaults will most likely not expose any indexable data vault-level or resource-level data.
- A Data Vault Directory Service (DVDS) (15) might exist to enable the lookup and resolution of Alice’s Data Vaults (7,10, 13) by various public data vault properties. Private and Secret Data Vaults will most likely not expose any public data vault properties and would not be locatable using the DVDS (15).
Acknowledgements
The above proposal for describing a Hub using the TDW Hub Architecture Reference Model (HUB-ARM) was inspired by Daniel Buchner’s verbal description of a Hub during the DIF SDS/CS call on Thursday, March 11, 2021 plus subsequent conversations on the DIF SDS/CS mailing list (Adrian Gropper).

Pingback: Trusted Digital Web: Trusted Content Storage Whitepapers | Hyperonomy Digital Identity Lab - hyperonomy.com