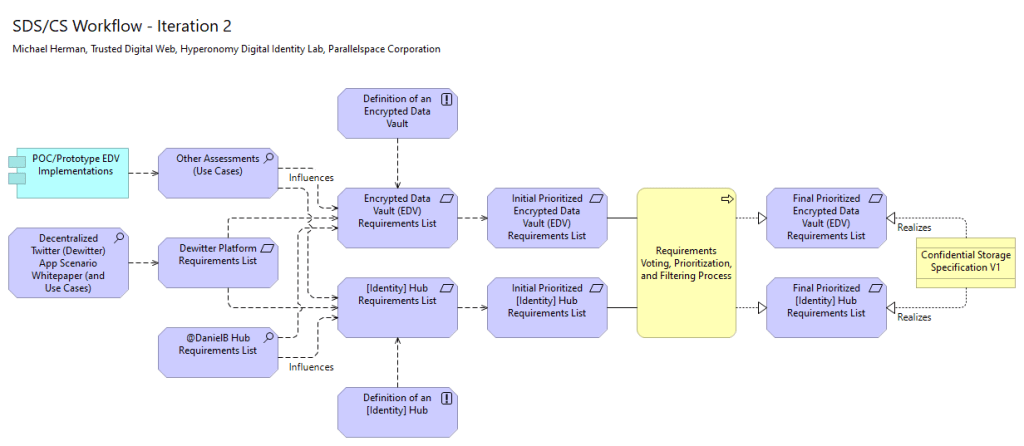
Click to the figure to enlarge it.
Copyright (c) 2021 Michael Herman (Alberta, Canada) – Creative Commons Attribution-ShareAlike 4.0 International Public License
https://creativecommons.org/licenses/by-sa/4.0/legalcode
I didn’t discover/understand I was a First Principles Thinker until relatively recently. Now, it’s my goto skill. Onward…
“Sometimes called “reasoning from first principles,” the idea is to break down complicated problems into basic elements and then reassemble them from the ground up. It’s one of the best ways to learn to think for yourself, unlock your creative potential, and move from linear to non-linear results.”
First Principles: The Building Blocks of True Knowledge (https://fs.blog/2018/04/first-principles/)
“I think it is most important to reason from first principles rather than by analogy. One of the ways we conduct our lives is we reason by analogy. We do this because something was like something else that was done or it was like what other people were doing. It’s mentally easier to reason by analogy rather than from first principles.”
First Principles Method Explained by Elon Musk (https://www.youtube.com/watch?v=NV3sBlRgzTI)
“You boil things down to the most fundamental truths
First Principles Method Explained by Elon Musk (https://www.youtube.com/watch?v=NV3sBlRgzTI)
And you say “what are we sure is true” or “as sure as possible, what is true”
And then “reason up from there”
That takes a lot more mental energy.”
Click on this video…

As well as this second video…
Video 2. The Most Powerful Way to Think | First Principles (https://www.youtube.com/watch?v=HZRDUZuIKg4)
I wager that most First Principles Thinkers are monarchs of their own belief system.
Filed under Uncategorized
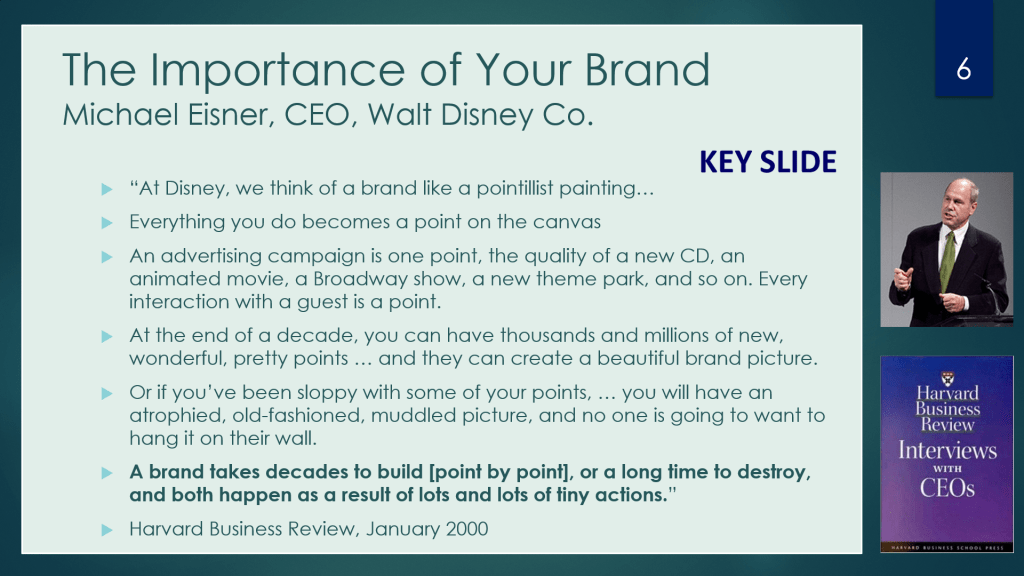
Download this presentation from here: The Rise and Fall of a Brand: Michael Eisner.
If you don’t have time, the following is the key slide.
Filed under Uncategorized
And voila, it worked first crack. Here are links to a couple of sample definitions:
Yesterday afternoon, I downloaded and imported the entire Sovrin Glossary V3 into Archi and the https://github.com/mwherman2000/tdw-glossary-1 repository. It contains all 249 SF Glossary terms and definitions plus a couple dozen of my own definitions (yes, the TDW Glossary supports ingesting multiple upstream glossaries and can create/refresh multiple downstream glossaries.)
Here are some screenshots:



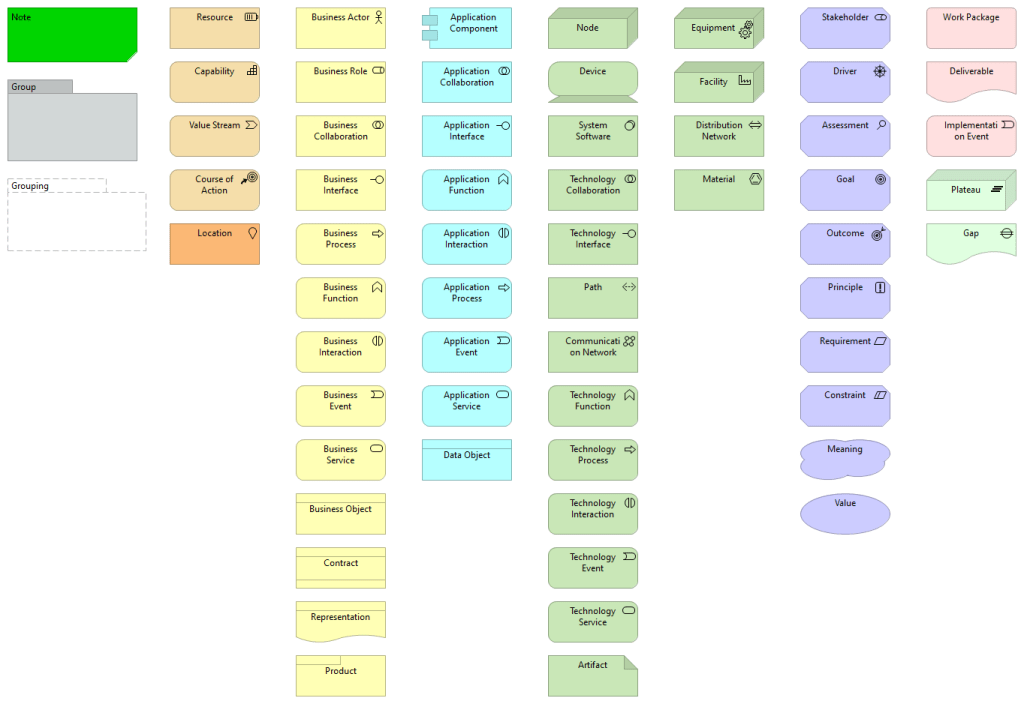
The Archi® modeling toolkit is targeted toward all levels of Enterprise Architects and Modelers. It provides a low cost to entry solution to users who may be making their first steps in the ArchiMate modeling language, or who are looking for an open-source, cross-platform ArchiMate modeling tool for their company or institution and wish to engage with the language within a TOGAF® or other Enterprise Architecture framework.
Archi open source modeler website (https://www.archimatetool.com/)
You can download and support the latest version of Archi from here: https://www.archimatetool.com/ .
You can download the latest version of the coArchi, Model Collaboration Plugin for Archi from here: https://www.archimatetool.com/plugins/#coArchi
Best regards,
Michael Herman
Sovrin Foundation Self-Sovereignist
Filed under Uncategorized
A generic Replication Pipeline is illustrated below.

Outbound Processing Service
Outbound Processing Service is responsible for capturing and recording Replication Events that occur in the Source Repository. Outbound Processing Service is controlled by Replication Maps which determine what Events need to be captured, packaged, and transferred to the Target Repository. Groups of Replication Events are packaged into two types of messages or objects: Queued Items and Replication Packages.
Queued Item
A Queued Item is a unit of work to be transferred to a Target Repository for remote execution. The Replication Web Service on a Target Repository is called to push a Queued Item from the Source Repository to a Target Repository.
Replication Package
A Replication Package is a collection of one or more Replication Events plus data about the changed information that is packaged in a format specific to the Replication Transport being used. When an Event is being processed, Outbound Processing Service calls the Source repository object model to extract the changed information from the Source Repository.
Package Transfer Service
The Package Transfer Service activity is responsible for the transfer and receipt of Queued Items and the downloading of Replication Packages (Packages) from the Source Repository to the Target Repository. Package Transfer is the process that sits between Outbound Processing Service (on the Source Repository) and Inbound Processing Service (on the Target Repository).
Inbound Processing Service
Inbound Processing Service is responsible for processing the Queued Items and Packages received and accepted by the Target Repository and applying them to the repository. The Queued Items and Packages are applied to the Target Repository content base by calling the Target Repository object model.
Filed under Uncategorized
Click here to download the whitepaper:


Version 0.28
Version 0.26
Version 0.25
Version 0.24
Filed under Uncategorized
Sovrin has many mission statements. The following is a summary of the Sovrin Foundation Mission Statement related text found on the Sovrin Foundation website.
M1. What is the Sovrin Foundation?
[Sovrin Foundation FAQ (https://sovrin.org/faqs/)]
The mission of the Sovrin Foundation is to create the Internet’s long-missing identity layer and provide a global public utility for digital identity to people, organizations, and things. The Sovrin Network enables you to personally curate and control your own collection of identity credentials by letting you selectively disclose your identity in a verifiable way.
M2. The Sovrin Alliance
[The Sovrin Alliance (https://sovrin.org/the-sovrin-alliance/)]
Marketplace Solution
The Sovrin Network enables people, organizations or IoT devices to prove things about themselves to anyone or anything, peer-to-peer, using data that the other party can verify. When anyone or anything is able to trust who or what it is dealing with online, massive amounts of friction can be removed, user experience can improve, and the transaction processes can be simplified.
Neutral Governance
The Sovrin Foundation is a 501(c)(4) nonprofit entity that provides the business, legal, and technical support for the Sovrin Network. Charged with administering the publicly created Governance Framework for the Sovrin Network, the Foundation is committed to transparency and neutrality.
Breakthrough Technology
Using the latest identity technology standards called Decentralized Identifiers (DIDs), the Sovrin Network allows for digital credentials to be privately issued, controlled, managed, and shared using a security standard called Zero Knowledge Proofs. The growth of the Sovrin Network partly depends on contributions from an active and supportive open-source development community.
Identity For All
Integral to the mission of the Sovrin Foundation, is to ensure everyone — regardless of circumstance — has access to the Sovrin Network. The Sovrin Foundation’s I4A council partners with NGOs, civil society organizations, and other groups promoting more inclusive identification systems to help bring identity network technology to populations who may not otherwise be served.
M3. People
[People (https://sovrin.org/team/)]
Mission
The Sovrin Foundation is a nonprofit organization established to promote the concept of internet identity for all and to administer the Governance Framework governing the Sovrin Network, a decentralized global public network enabling self-sovereign identity on the internet. The Sovrin Network is operated by independent Stewards and uses the power of a distributed ledger to give every person, organization, and thing the ability to own and control their own permanent digital identity.
M4. Sovrin Stewards: Helping create self-sovereign identity for all
[Sovrin Stewards: Helping create self-sovereign identity for all (https://sovrin.org/sovrin-stewards-helping-create-self-sovereign-identity-for-all/)]
The Sovrin Foundation’s mission is to provide people and organizations with access to self-sovereign digital identity, and it does this by building, administering, and promoting a global, decentralized, public identity utility called the Sovrin Network.
Filed under Uncategorized
Click here to download the whitepaper:
Filed under Uncategorized
Create your own magic with Web 7.0™ / TDW AgenticOS™. Imagine the possibilities.
Copyright © 2021-2025 Michael Herman (Bindloss, Alberta, Canada) – Creative Commons Attribution-ShareAlike 4.0 International Public License
Web 7.0™, TDW AgenticOS™ and Hyperonomy™ are trademarks of the Web 7.0 Foundation. All Rights Reserved.
For a complete list of 20+ technology adoption models, checkout: Technology Adoption Models: A Comprehensive Guide.

[Model 2d] Michael Herman (https://www.linkedin.com/in/mwherman/)
ADKAR Change Management Model (https://www.prosci.com/adkar/adkar-model)
Filed under Uncategorized
Click here to download this Parallelspace Corporation Technical Note: PSN TN0028: SPS2003 XML Import-Export “Operation” Attribute
The technical note proposes the addition of an operation attribute to the XML emitted for each exported item by the SPS2003 Upgrade.exe tool. The schema for the operation attribute would include the following operations:
| operation Attribute Values | Description | Pre-delete Existing Item | Create New Item |
| operation=”delete” | Delete deletes an existing item imported into SPS2003 during a previous execution of the Import tool; or fails if the item doesn’t exist. | No | No |
| operation=”remove” | Delete deletes an existing item imported into SPS2003 during a previous execution of the Import tool, if it exists. | No | No |
| operation=”create” | Create creates a new instance of the exported item; or fails if the item already exists (see replace, update and add) | No | Yes |
| operation=”replace” | Replace replaces an existing item imported intoSPS2003 during a previous execution of the Import tool by executing a Delete followed by a Create; or fails if the item doesn’t exit. | Yes | Yes |
| operation=”add” | Add a) creates a new instance of the exported item if the item does *not* exist; or b) replaces an item if the item was imported into SPS2003 during a previous execution of the Import tool. This operation shouldn’t fail based on previous import operations | a) No b) Yes | a) Yes b) Yes |
| operation=”merge” | Add a) creates a new instance of the exported item if the item does *not* exist; or b) updates an item if the item was imported into SPS2003 during a previous execution of the Import tool. This operation shouldn’t fail based on previous import operations | a) No b) No | a) Yes b) No |
| operation=”update” | Update adds or replaces the values of selected attributes of an existing item imported intoSPS2003 during a previous execution of the Import tool; or fails if the item doesn’t exit. | No | No |
| operations=”ignore” | Processing for this item is skipped. The contents of the item are ignored. | n/a | n/a |
Filed under Uncategorized